


Your employees adopted 40 AI tools last quarter. You approved only three. The other 37 hold OAuth tokens with read and write access to core SaaS platforms, yet none appear in your quarterly access review. That is AI sprawl, and by the time it surfaces in an incident report, the damage is often already measured in exposed records, unauthorized access, and financial loss.
This article outlines a four-layer detection framework for identifying AI sprawl at each stage, from the first unauthorized OAuth connection to uncontrolled agent growth, posture drift, and the anomalous activity that can precede a breach.
WHAT YOU'LL LEARN
Navigate to: Overview -> AI Governance -> AI Discovery -> App Detail -> Graph
Detection begins on the Overview dashboard, where the posture score, top failing checks, weakest applications, and security domain rankings provide initial signals that AI sprawl may be growing. From there, the investigation moves deeper: into AI Discovery to identify connected AI tools, into App Detail to understand what each tool can access, and into the Graph view to visualize the full connection web across SaaS applications.
*Security posture metrics such as Microsoft Secure Score measure security health on a 0–100 scale, with higher values indicating more recommended protections implemented. Scores below roughly 50% often indicate substantial gaps in configuration or security controls.
ACTION: Run this drill-down weekly. Start at Overview. If the AI Security domain score drops below 50% or the posture score trends downward, navigate to AI Discovery, filter by Gen AI, and prioritize apps with high user counts that remain in To Review status.I plugins inherit permissions from the authorizing user. If an administrator grants access, the plugin inherits admin-level scopes. Always verify who authorized high-risk plugins first.
Navigate to: AI Governance -> AI Agents
The Overview indicates an issue. The AI Agents Inventory shows exactly what. This module focuses on agentic AI, autonomous agents that take actions, make decisions, and interact with SaaS applications on behalf of users. These agents carry the highest permission risk because they do more than read data. They can perform actions across connected systems.
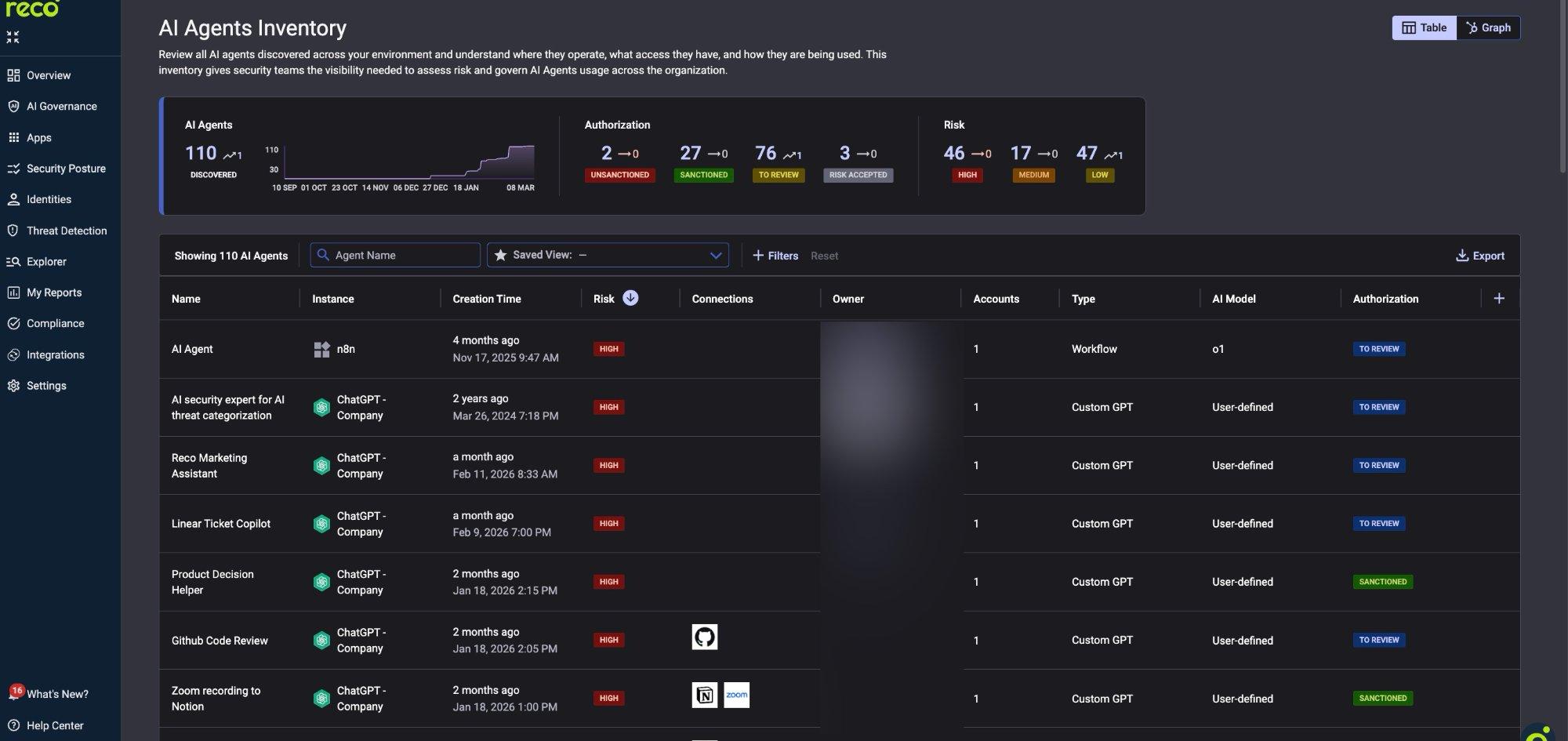
The dashboard shows agent growth over time, helping you identify adoption surges. The table provides per-agent details, including platform (n8n, ChatGPT), type (Workflow, Custom GPT), AI model, SaaS connections, and authorization status.
Switch to the Graph view to visualize the full connection web. Click any agent to see its scopes and actions. The broader AI Governance navigation (AI Discovery, Connected AI Apps, AI Agents, AI Models, AI Posture Checks, AI Dashboard) provides additional detection layers.
ACTION: Sort by Risk (High first) and filter by To Review. Agents with multiple connections and recent creation dates represent the highest unreviewed risk. Assign an authorization status within seven days of discovery.
Navigate to: AI Governance -> AI Posture Checks
Detection without enforcement is only reporting. Posture checks run every 24 hours against more than 3,200 configurations. Filter by the Gen-AI Security and IAM domains to focus on AI-specific controls.
Reco also provides built-in AI agents for security teams (Settings → Reco AI Agents Management), including Response Plan for application remediation, identity analysis agents, and Alert Story for contextual summaries. These agents are enabled by default and can be toggled on or off at any time.
ACTION: Enable every CRITICAL and HIGH check in Gen-AI Security and IAM. For each TO REVIEW result, use the detail modal for step-by-step remediation and compliance mapping.s of discovery.
Navigate to: Threat Detection -> Policy Center
Posture checks detect configuration drift on a daily basis. Threat Detection identifies behavioral anomalies within approximately 15 minutes.
Start with 15 to 20 AI-relevant policies in Preview mode. Promote them to On after two to four weeks of validated signal quality.
CAUTION: Do not enable all 400+ policies at once. Excessive alerting can overwhelm detection programs faster than AI sprawl itself. Start in Preview mode, validate signal quality, then promote policies to On.
AI sprawl compounds quietly. This framework detects it at every stage: Overview surfaces the signal, AI Agents reveal the entities involved, Posture Checks enforce the guardrails, and Threat Detection identifies anomalous behavior. Run all four layers, and AI sprawl becomes a governance challenge rather than a breach.
AI adoption is expanding faster than most security programs can track. New tools, plugins, and autonomous agents appear daily, often with OAuth permissions that extend deep into core SaaS platforms. Without a structured detection approach, these integrations accumulate quietly until they become part of an incident investigation. A layered detection strategy helps security teams stay ahead of that risk.
By continuously monitoring signals in the Overview dashboard, inventorying agents, enforcing posture guardrails, and detecting anomalous behavior, organizations can turn AI sprawl from an invisible exposure into a manageable governance problem. The earlier these signals are detected, the smaller the blast radius when something goes wrong.

Gal is the Cofounder & CPO of Reco. Gal is a former Lieutenant Colonel in the Israeli Prime Minister's Office. He is a tech enthusiast, with a background of Security Researcher and Hacker. Gal has led teams in multiple cybersecurity areas with an expertise in the human element.
