Model Context Protocol (MCP) Is Rewiring SaaS Trust, One Agent Action at a Time



The Model Context Protocol (MCP) is an emerging standard that bridges AI agents (like LLM-based assistants) to external SaaS tools and APIs. In essence, MCP provides a unified interface for AI agents to access SaaS data and perform actions on a user’s behalf in a structured, controlled way.
This unlocks richer workflows and data sharing: an agent could fetch files from Google Drive, update Salesforce records, or send Slack messages, all automatically and in real-time. With organizations adopting AI copilots that plug into hundreds of cloud apps, MCP has quickly become the plumbing that makes these SaaS-to-SaaS integrations possible.
By giving AI agents direct API access, MCP is transforming SaaS identity. Instead of just users and admins, we now have non-human identities (NHIs) like AI bots acting within our SaaS environments. These agents operate at machine speed and can make independent decisions, fundamentally changing how trust and permissions are managed.
Security teams cannot afford to ignore MCP’s rise, it’s enabling powerful new automation, but it also introduces new risks and a new identity layer that must be governed.
The Hidden Risk - Identity Drift at Machine Speed
The primary risk of AI agents is how they can expand SaaS trust paths over time. Once authorized, an agent can chain multiple tools and services together, request new API scopes, or even get reassigned to different backend servers, all without human oversight.
Over days and weeks, an agent might quietly accumulate access to far more data and systems than initially intended. This silent expansion of privileges is akin to classic privilege creep, but occurring at machine speed. In traditional IAM, privilege creep might take months or years of role changes; with autonomous agents, an equivalent identity drift can unfold in hours.
Agents can spawn or integrate new tools dynamically, often faster than security teams can react. Without governance, an AI agent that started with read access to one SaaS app might chain into write access on another, blurring trust boundaries across apps. It’s a new challenge: security teams need to manage machine identities that evolve much faster than human ones, and ensure SaaS trust paths don’t sprawl out of control.
Now, let’s summarize the main risks introduced by MCP-based trust paths:
Weak Authentication
A lot of MCP implementations lack authentication upfront. For instance, early MCP servers were often deployed without even basic authentication or input validation. If an agent integration isn’t strongly authenticated and scoped, attackers or unauthorized agents can invoke it freely. Moreover, if an agent is simply using a human user’s OAuth token, it inherits all that user’s privileges without additional checks, which can be dangerously broad.
Connector Supply-Chain Exploits
AI agents rely on connectors and tool descriptions to interact with apps. If one of these connector packages is compromised or a malicious tool is introduced, an agent might execute harmful actions unknowingly. We’ve seen how a single chatbot plugin became an attack vector to breach multiple downstream systems. The lack of integrity checks on MCP tools means an attacker who poisons one connector could potentially leverage it to traverse across connected apps, installing malware or siphoning data via the trusted link.
Data Leakage at Scale
By design, MCP lets agents directly query data stores via APIs. Without strict scope limits, an agent might pull far more data than a user would ever see. For example, an AI writing assistant with access to your Google Drive could accidentally (or intentionally, if compromised) read through entire document repositories. MCP servers often grant the AI tool the same data permissions as the user who set it up, which can result in much broader data access than intended.
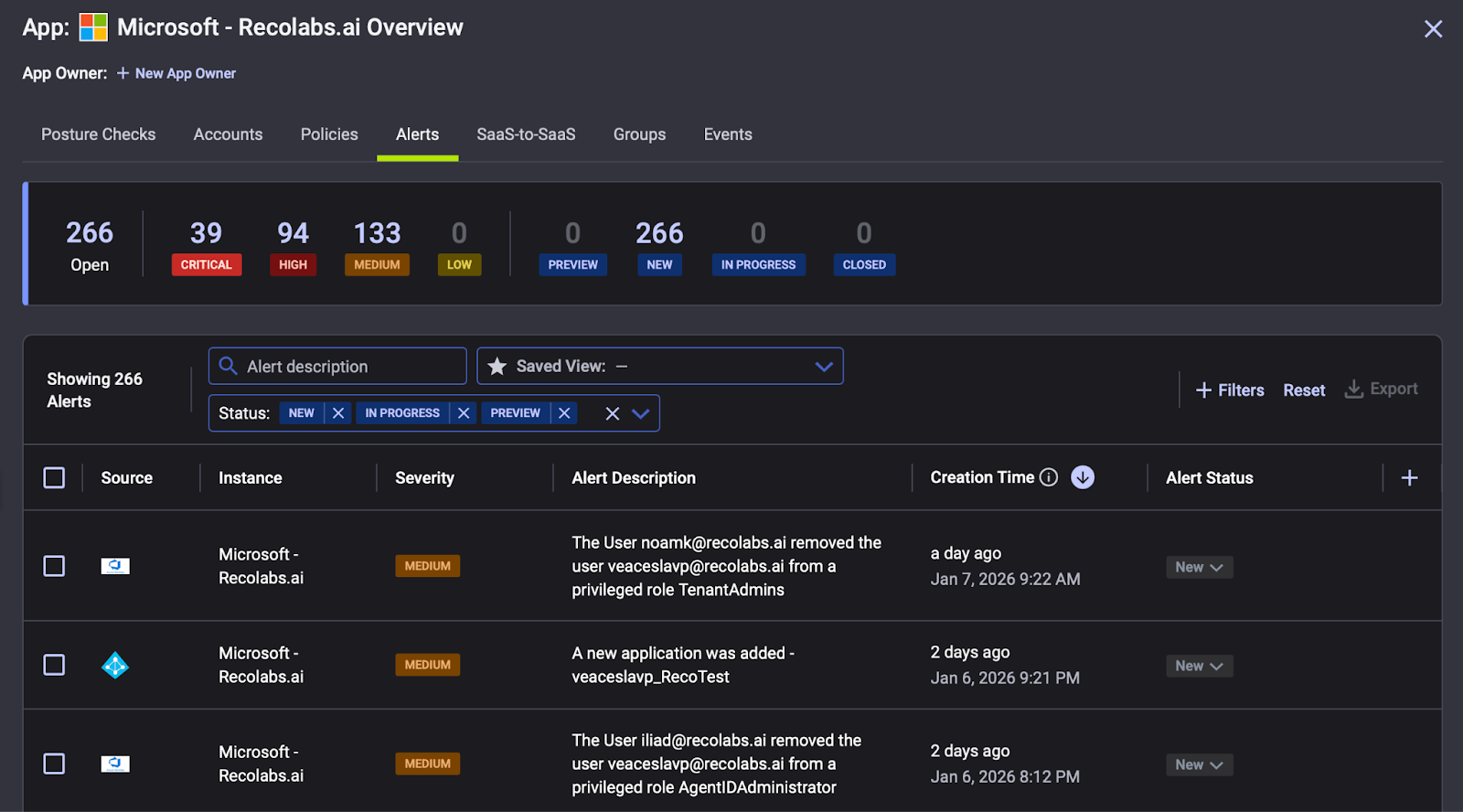
Invisible & Unmonitored Access
Perhaps most troubling, security teams lack visibility into these app-to-app interactions. When an agent is authorized to connect two SaaS apps, it often does so via tokens and API calls that bypass traditional user activity logs. Standard CASBs or SIEM rules might miss an AI service account making API calls at 2 AM, because it doesn’t trigger the same alerts a human login would. Attackers are aware of this, so they can abuse legitimate agent credentials to exfiltrate data while flying below the radar of tools that watch the front door but not these side-door agent connections.
MCP Agents - Hardening Checklist for SaaS Trust Paths
To govern AI agents and their SaaS access, organizations should establish a hardened security framework. Essentially, an identity and access governance model for MCP. Below is a practical checklist to get ahead of identity drift and reduce the blast radius if an agent goes rogue:
Use the Right OAuth Grant Type
When integrating an AI agent with a SaaS app, use the least privileged OAuth flow possible. For example, if an agent only needs user-level access for a single task, prefer delegated user OAuth (on-behalf-of the user) over granting it a privileged admin API key. Avoid giving an agent a full admin consent unless absolutely necessary. This ensures the agent doesn’t start with a master key to your data when a limited-use key would suffice.
Enforce Least Scope per Task
Design agent permissions on a need to know and need to do basis. Just as you wouldn’t give an employee access to every SaaS app for one job, ensure each agent is scoped strictly to the APIs and data required for its specific function. This may mean creating granular, task-specific roles or OAuth scopes. For instance, an agent set to archive emails shouldn’t also have permissions to delete contacts. Regularly review what each agent is actually doing versus what it’s allowed to do. If there’s a mismatch, tighten the scope.
Time-Box Your Tokens
Don’t let AI agents have evergreen credentials. Use short-lived, ephemeral tokens that expire quickly, forcing agents to re-authenticate or fetch new tokens frequently. By implementing tight token lifespans, you limit the window in which an attacker could exploit a stolen credential. Instead of a static API key embedded in an agent’s code, use a secure vault and have the agent request a fresh access token right before it runs a task, with that token auto-expiring soon after. This approach contains the damage from leaked or abused tokens, much like a short-lived hotel key that prevents long term access.
Bind Every Agent to a Human Owner
Every non-human identity needs an accountable human identity behind it. In practice, that means tagging each agent’s service account with an owner (and ideally recording who or what process launched the agent). Implement on-behalf-of logging: any action an agent takes should be linked in audit logs to the human who authorized it (e.g., tie the agent’s token back to the user’s ID). Ownership tagging also helps with lifecycle: when an employee leaves or a project ends, you can review and retire their agents.
Take Your Next Steps With Reco
On top of the checklist above, it’s also a good idea to adopt a Dynamic SaaS Security Platform that can continuously discover and govern MCP-based trust paths as they appear. Reco makes MCP agent to SaaS access observable and governable, so security teams can validate trust paths, enforce ownership, and control permission drift as adoption scales.
Automatically Discover All MCP Usage
Reco continuously detects every instance of MCP in use across your environment without manual input. As soon as an AI agent establishes a new SaaS integration via MCP, it’s immediately identified, eliminating blind spots in your entire cloud app ecosystem.
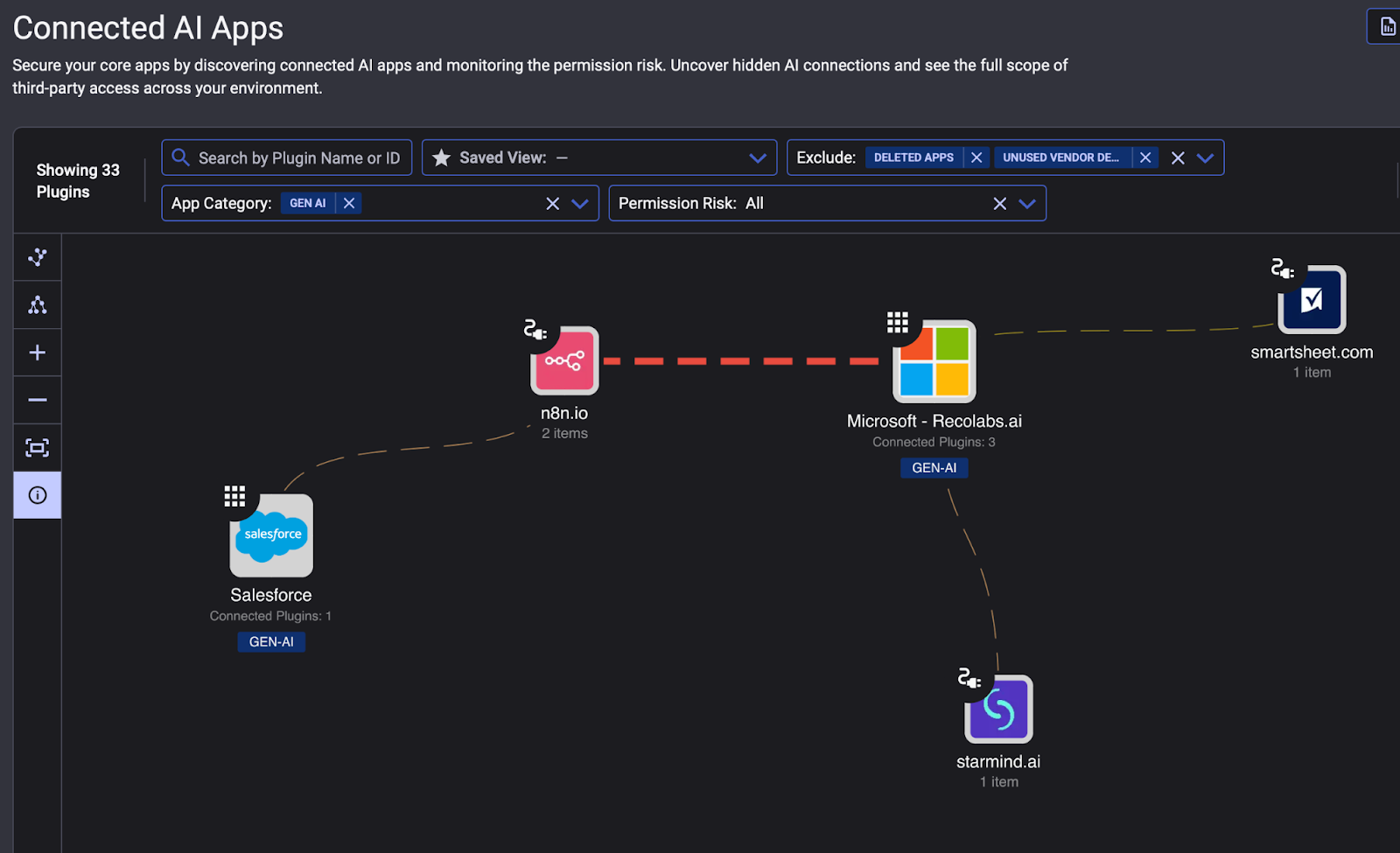
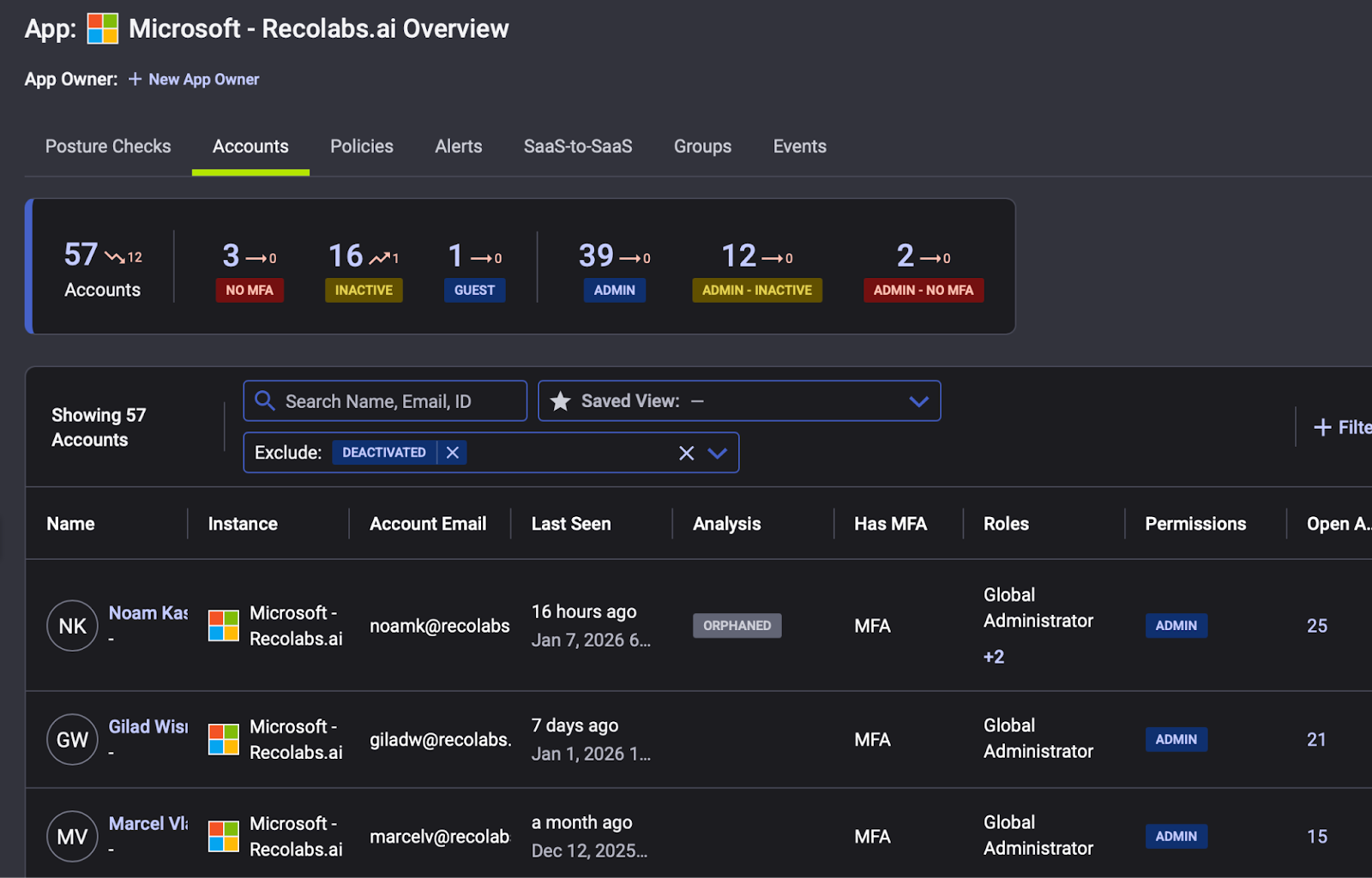
Trace Each Connection to a Real Identity
Every agent-initiated connection is tied back to the actual identity behind it, whether that’s a human user, a service account, or another non-human identity (NHI). By mapping every action to an owner, Reco ensures accountability for AI-driven activities that would otherwise operate under the radar.
Monitor Every Agent Trust Path in Detail
Reco watches both sides of each agent-to-app interaction. Reco logs which SaaS application an agent accesses, which protocol (e.g. MCP) is used, and the specific token/credentials authorizing the exchange, on both the calling agent (client) and target service (server) side. This full context means MCP is no longer an invisible backchannel; security teams can validate and control every aspect of the connection.
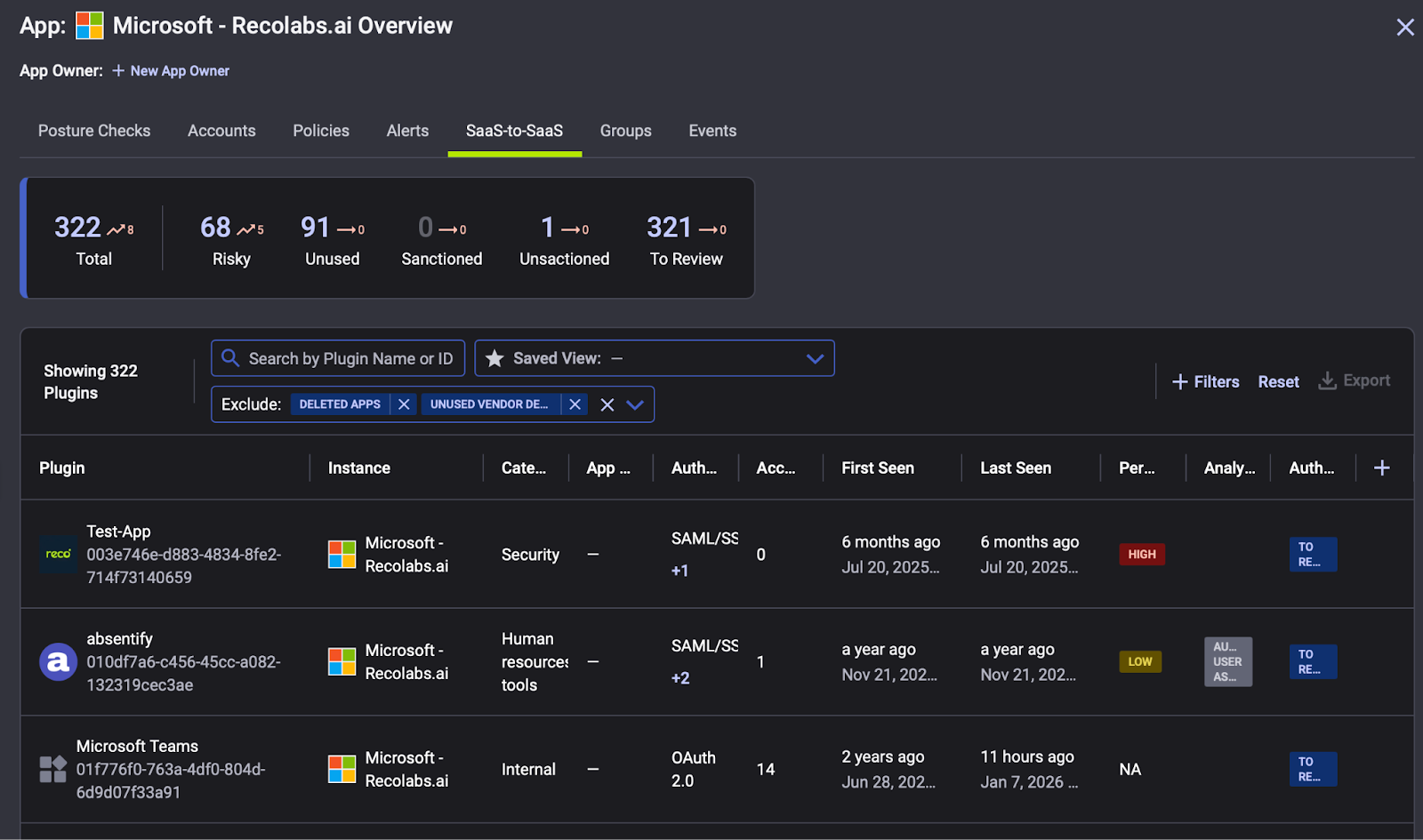
Track Evolving Agent Permissions
Reco also helps teams stay ahead of how agent permissions evolve. Because agents can request access in unpredictable ways, Reco tracks the scopes and permissions being granted and used, helping teams enforce least privilege without breaking workflows. With coverage across 225 plus SaaS apps, Reco can see these MCP trust paths wherever they form.
MCP unlocks AI. Reco secures it - Request a Demo: Get Started With Reco.

Gal Nakash
ABOUT THE AUTHOR
Gal is the Cofounder & CPO of Reco. Gal is a former Lieutenant Colonel in the Israeli Prime Minister's Office. He is a tech enthusiast, with a background of Security Researcher and Hacker. Gal has led teams in multiple cybersecurity areas with an expertise in the human element.

Gal is the Cofounder & CPO of Reco. Gal is a former Lieutenant Colonel in the Israeli Prime Minister's Office. He is a tech enthusiast, with a background of Security Researcher and Hacker. Gal has led teams in multiple cybersecurity areas with an expertise in the human element.



%201.svg)











%201.svg)









.svg)