Top 10 Shadow AI Detection Tools for Enterprise Security in 2026

Shadow AI is no longer a fringe problem. It is showing up across SaaS environments through copilots, browser-based tools, and OAuth-connected apps that employees adopt without oversight. Unlike traditional shadow IT, these tools interact directly with sensitive data and identities. Most security teams lack clear visibility into where this usage happens. That gap is driving demand for shadow AI detection tools that can uncover AI activity, map risk, and bring governance back into SaaS environments.
10 Best Shadow AI Detection Tools for Enterprise Visibility and Control
To address these visibility gaps, organizations are turning to specialized shadow AI detection tools that go beyond traditional SaaS discovery. These platforms provide deeper insight into AI usage, data exposure, and identity-driven risk across modern SaaS environments.
1. Reco
Reco is an identity-centric SaaS security platform that helps organizations detect and manage shadow AI across their SaaS environments. It combines SaaS discovery, identity intelligence, and data exposure insights to give security teams a clear understanding of AI usage, access patterns, and associated risk across users, applications, and integrations.
AI App and Copilot Visibility: Discovers AI apps, copilots, and embedded AI features across SaaS platforms, including tools connected through OAuth grants, APIs, and third-party integrations.
Identity and Access Context: Maps AI activity to user and non-human identities, exposing access levels, permission scope, and how these tools interact with enterprise data.
2. Torq (AI Security Automation & Detection)
Torq is a security automation platform that focuses on orchestrating detection and response across SaaS, cloud, and security tools. While it is not a dedicated shadow AI discovery platform, it helps operationalize AI-related signals by connecting data sources, enriching alerts with identity context, and automating investigation and remediation workflows across the security stack.
AI App and Copilot Visibility: Provides indirect visibility into AI-related activity through integrations with SaaS, cloud, and security tools, surfacing signals tied to AI usage within broader workflows.
Identity and Access Context: Enriches alerts with identity data from connected systems, helping teams understand which users or accounts are involved in security events, including those related to AI usage.
3. Rezonate (Identity-Centric AI Risk Detection)
Rezonate, now part of Silverfort, is an identity security platform that focuses on mapping access, permissions, and relationships across cloud and SaaS environments. It provides deep visibility into how users and service accounts interact with applications and data, helping security teams identify overprivileged access and risky identity behavior that may expose enterprise systems, including AI-enabled services and integrations.
AI App and Copilot Visibility: Does not provide dedicated AI discovery, but surfaces potential AI-related exposure through visibility into SaaS applications, integrations, and access activity across the environment.
Identity and Access Context: Maps human and non-human identities, access paths, and permissions across cloud and SaaS environments, helping identify excessive access and risky identity behavior.
4. Veza (Authorization and Access Intelligence for AI Apps)
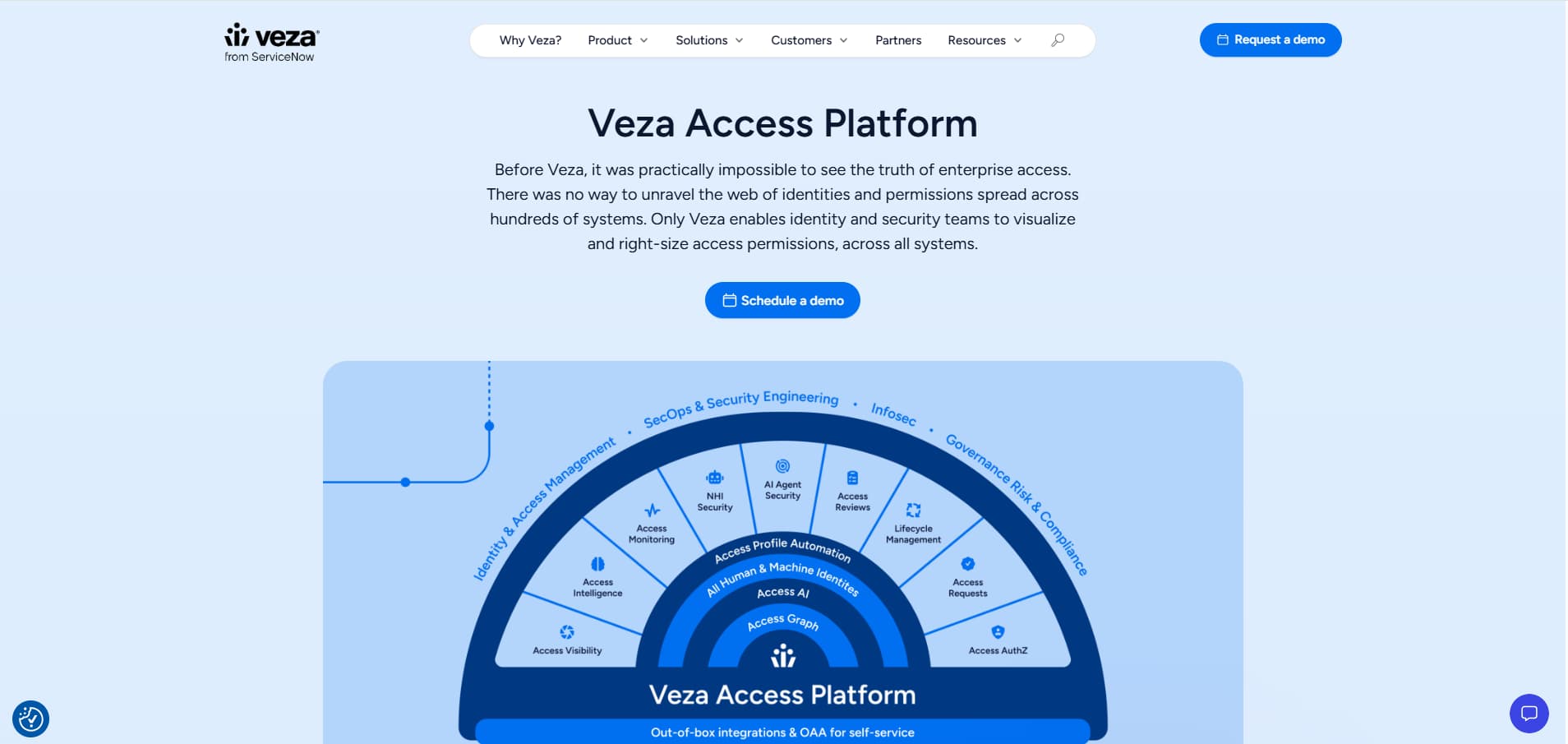
Veza is an identity security platform that focuses on understanding and controlling who can access what across SaaS, cloud, and data systems. Its core capability is the Access Graph, which maps identities, permissions, and data access relationships, giving security teams a unified view of authorization across environments.
AI App and Copilot Visibility: Provides visibility into AI agents and AI-enabled services by mapping what data and systems these agents can access, helping organizations understand and govern AI-related access across environments.
Identity and Access Context: Maps human and non-human identities, permissions, and access paths across SaaS, cloud, and data systems, enabling teams to analyze who can access what data and enforce least-privilege controls.
5. Astrix Security (Non-Human Identity and SaaS Integration Security)
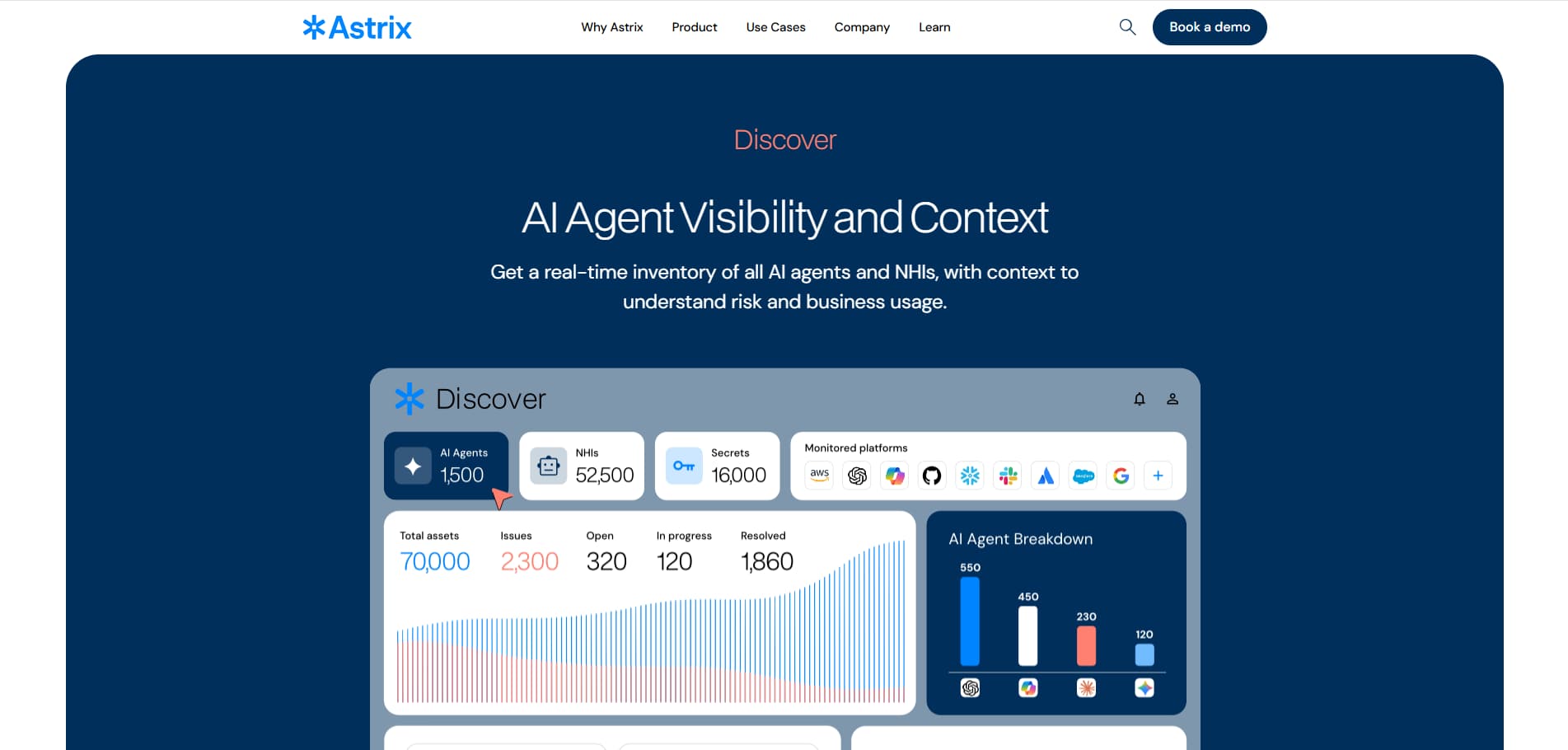
Astrix Security is a SaaS security platform focused on securing non-human identities and third-party integrations across SaaS environments. It provides visibility into service accounts, OAuth applications, and machine-to-machine connections, helping organizations reduce risk from overprivileged integrations and unmanaged access across their SaaS ecosystem.
AI App and Copilot Visibility: Does not provide dedicated AI discovery, but surfaces potential AI-related exposure through visibility into SaaS integrations, OAuth apps, and service connections that may include AI-powered tools or automated agents.
Identity and Access Context: Maps non-human identities, service accounts, and integration permissions across SaaS environments, helping teams identify excessive access and risky third-party connections.
6. Lumos (Identity Governance and App Access Visibility)
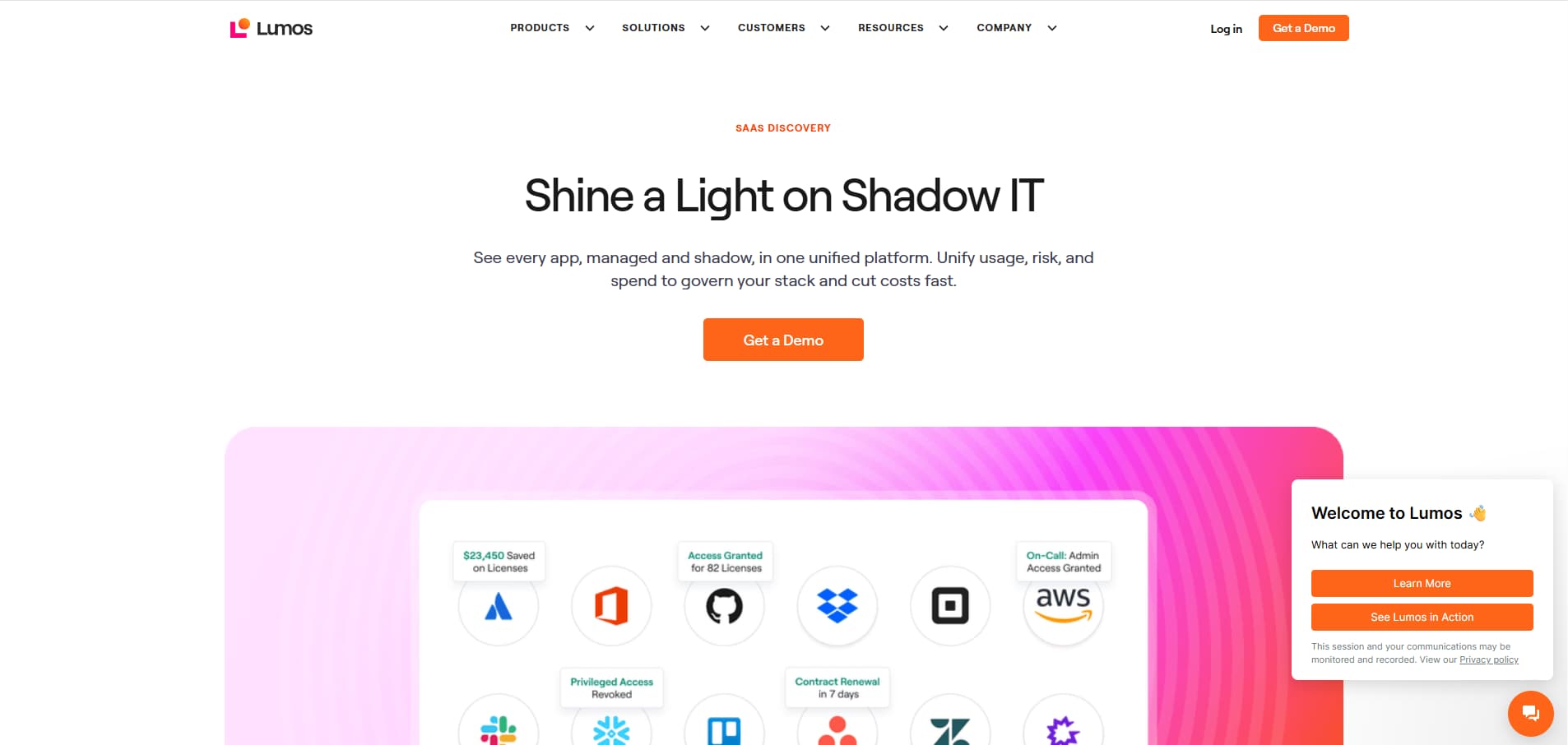
Lumos is an identity governance and SaaS access management platform that helps organizations gain visibility into application usage, access permissions, and user activity across their SaaS stack. It enables security and IT teams to manage user access, enforce least-privilege principles, and reduce risk from unmanaged or overprovisioned applications.
AI App and Copilot Visibility: Provides visibility into AI-related usage through SaaS application discovery and access monitoring, helping identify AI-enabled features and tools used across the environment.
Identity and Access Context: Maps user identities, roles, and access permissions across SaaS applications, enabling teams to understand who has access to what and enforce appropriate access controls.
7. Nudge Security (Shadow IT and SaaS Discovery)
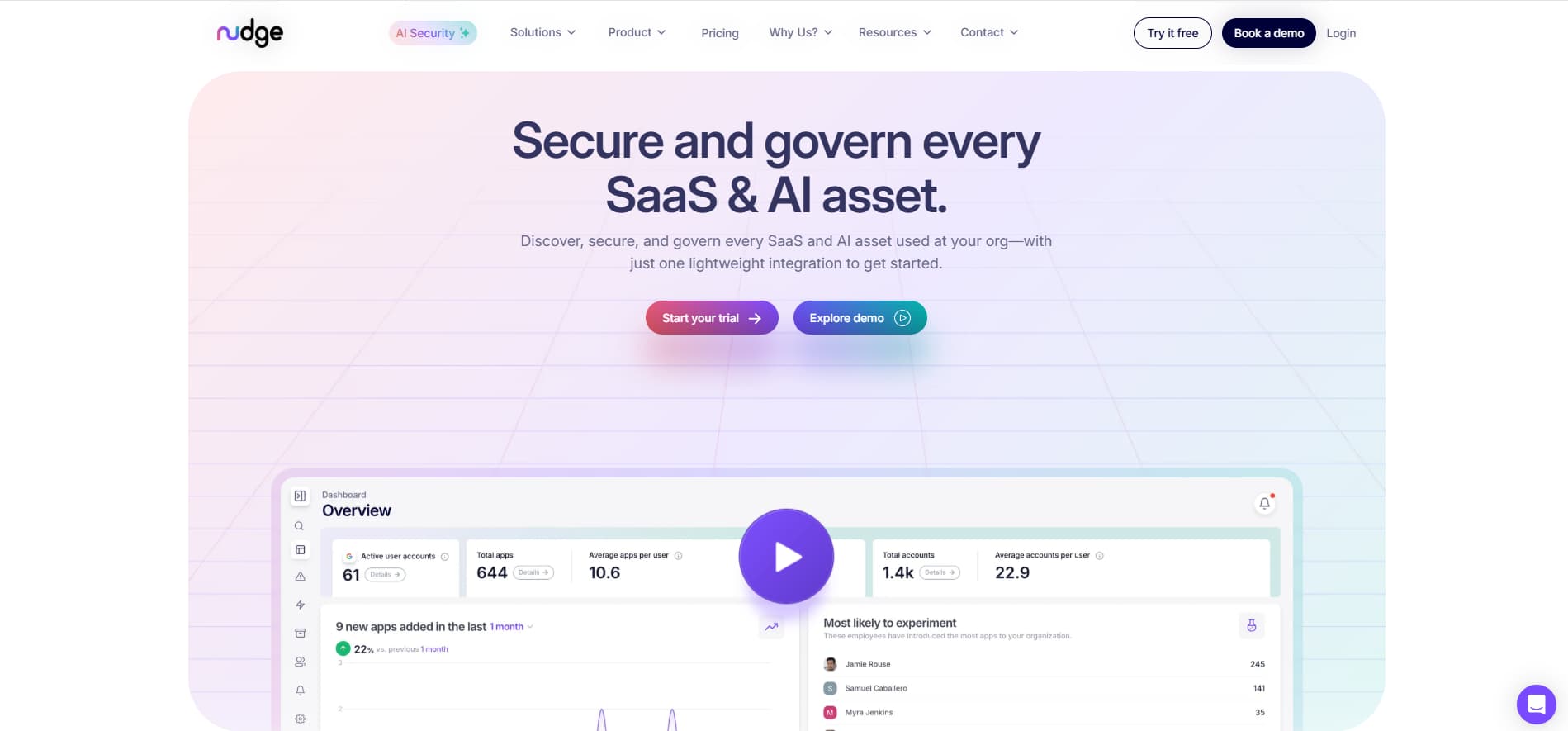
Nudge Security is a SaaS security platform focused on discovering and managing shadow IT across cloud environments. It provides continuous visibility into application usage, user activity, and third-party integrations, helping security teams identify unauthorized tools and reduce risk across their SaaS ecosystem.
AI App and Copilot Visibility: Identifies AI-related tools and usage through SaaS discovery and activity monitoring, helping surface unauthorized AI apps, browser-based tools, and integrations adopted without IT oversight.
Identity and Access Context: Maps user identities, accounts, and access relationships across discovered applications, enabling teams to understand who is using which tools and assess associated risk.
8. BetterCloud (SaaS Operations and Usage Visibility)
BetterCloud is a SaaS management platform that provides visibility into application usage, user activity, and integrations across cloud environments. It helps IT and security teams manage SaaS operations, enforce policies, and monitor how applications interact with organizational data.
AI App and Copilot Visibility: Provides visibility into AI-related usage through SaaS discovery, OAuth app monitoring, and integration tracking, helping identify AI-enabled tools and features used across the environment.
Identity and Access Context: Maps user accounts, permissions, and access across SaaS applications, enabling teams to understand how users interact with apps and enforce access policies.
9. Trelica by 1Password (SaaS Discovery and Spend Visibility)
Trelica by 1Password is a SaaS management platform that helps organizations discover, manage, and optimize application usage across their environment. It provides visibility into SaaS adoption, user activity, and spend, enabling IT and security teams to control unauthorized applications and improve governance.
AI App and Copilot Visibility: Identifies AI-related tools and usage through SaaS discovery and application tracking, helping surface unauthorized AI apps and features adopted across the organization.
Identity and Access Context: Maps user accounts, access permissions, and application usage across SaaS tools, enabling teams to understand who is using which applications and manage access accordingly.
10. Productiv (SaaS Intelligence and Shadow App Monitoring)
Productiv is a SaaS intelligence platform that helps organizations gain visibility into application usage, user activity, and data flows across their SaaS ecosystem. It enables IT and security teams to monitor adoption, assess risk, and optimize how applications are used across the organization.
AI App and Copilot Visibility: Provides visibility into AI-related tools and features through SaaS usage monitoring and application discovery, helping identify unauthorized AI apps and embedded AI capabilities across the environment.
Identity and Access Context: Maps user activity, application access, and usage patterns across SaaS tools, enabling teams to understand how users interact with applications and evaluate associated risk.
Shadow AI Detection Tools Comparison Overview
The table provides a quick comparison of how each platform approaches shadow AI detection, deployment, and ideal use cases:
Key Capabilities to Look for in Shadow AI Detection Tools
Before selecting a solution, it is important to understand which capabilities actually matter for detecting and managing shadow AI across SaaS environments. The features below define how effectively a platform can provide visibility, context, and control.
- Continuous Discovery of AI Apps, Agents, and Copilots: Continuously identifies AI tools, embedded features, and autonomous agents across SaaS environments, including those connected through OAuth, APIs, and third-party integrations.
- Visibility Into SaaS-to-AI Connections and Data Flows: Maps how AI tools interact with SaaS applications and tracks the movement of sensitive data between systems, helping teams understand where exposure may occur.
- Identity-Centric Risk Detection Across Users and Non-Human Identities: Correlates AI activity with both human users and non-human identities, providing context into access levels, permissions, and behavioral risk.
- OAuth Grant and Third-Party App Governance: Monitors and manages OAuth permissions and third-party integrations, helping prevent overprivileged access and reduce risk from unauthorized AI connections.
- Contextual Risk Scoring and Prioritization: Analyzes activity, data exposure, and access patterns to prioritize high-risk AI usage, enabling security teams to focus on the most critical threats.
- Real-Time Alerts for Unauthorized AI Usage: Detects suspicious or unauthorized AI activity as it happens and generates alerts to support immediate investigation and response.
- Integration With Existing SaaS and Security Stacks: Connects with identity providers, SaaS platforms, and security tools to enrich visibility, streamline workflows, and enable coordinated response actions.
How to Choose the Right Shadow AI Detection Tool for Your Organization
Selecting the right solution depends on how AI is used across your environment and the level of visibility and control your security team requires. The table below outlines key evaluation criteria and what to look for in each area:
How Reco Detects and Secures Shadow AI Across SaaS Environments
Reco approaches shadow AI detection by combining SaaS discovery, identity context, and data exposure insights into a unified platform. This allows security teams to move beyond basic visibility and gain actionable control over how AI tools interact with users, applications, and sensitive data.
- Continuous Discovery of Shadow AI Apps, Agents, and Copilots Across SaaS: Continuously identifies AI tools, copilots, and embedded AI features across SaaS environments with application discovery, including those connected through OAuth, APIs, and third-party integrations.
- SaaS-to-AI Connection Mapping Across Apps, Identities, and Integrations: Maps how AI tools connect to SaaS applications, user accounts, and integrations with the SaaS app factory, providing a clear view of relationships and data pathways across the environment.
- Identity-Centric Visibility Into User and Non-Human AI Activity: Connects AI usage to both human and non-human identities with identity and access governance, giving teams clarity into access levels and exposure risk.
- Detection of Risky OAuth Grants and Third-Party AI Integrations: Flags overprivileged OAuth connections and risky third-party integrations with identity threat detection and response, reducing the risk of unauthorized data access.
- Contextual Risk Insights Based on Data Exposure and Access Patterns: Evaluates how sensitive data is accessed and shared through AI interactions with data exposure management, helping prioritize real risk over noise.
- Real-Time Monitoring of AI Usage Across Enterprise SaaS Ecosystems: Tracks AI activity across SaaS environments in real time with SaaS posture management and compliance, enabling faster detection and response.
Conclusion
Shadow AI is becoming a core part of how teams operate across SaaS environments. The challenge has shifted toward maintaining continuous visibility into how AI tools interact with data, identities, and business workflows. Organizations that rely on deeper, identity-aware, and context-driven detection gain a clear advantage in understanding and managing this evolving risk surface.
The path forward is about controlling AI with precision while supporting innovation. Security teams need platforms that connect discovery, access, and data exposure into a single, actionable view. As AI adoption accelerates, the ability to monitor, understand, and govern its use across SaaS environments will shape the overall strength of an organization’s security posture.
What makes shadow AI different from traditional shadow IT?
Shadow AI refers specifically to the use of AI tools and capabilities without IT oversight, while shadow IT includes any unapproved technology. The distinction matters because AI tools actively process and generate data.
- AI tools can ingest, transform, and store sensitive data in real time
- Many AI features are embedded inside approved SaaS apps, making them harder to detect
- AI introduces risks related to data exposure, automation, and decision-making
How do organizations detect unauthorized AI tool usage across SaaS apps?
Organizations detect shadow AI by combining SaaS visibility, identity context, and monitoring of integrations across their environment.
- Discover AI tools through SaaS application usage and OAuth connections
- Monitor API activity and third-party integrations
- Track user behavior and data movement patterns
- Correlate activity across users, applications, and access permissions
What are the biggest risks associated with shadow AI adoption?
Shadow AI introduces security, compliance, and operational risks when used without proper governance.
- Unauthorized access to sensitive data through AI tools
- Data leakage via prompts, file uploads, or integrations
- Overprivileged OAuth grants and third-party access
- Limited visibility and lack of auditability
How does Reco identify shadow AI across SaaS environments?
Reco identifies shadow AI by combining SaaS discovery, identity context, and data exposure insights across SaaS environments.
- Detects AI apps and integrations using application discovery
- Maps access and permissions through identity and access governance
- Flags risky behavior with identity threat detection and response
Can shadow AI detection tools track data exposure through AI interactions?
Yes, advanced platforms can track how sensitive data is accessed, shared, and exposed through AI tools and integrations.
- Monitor data flows between SaaS apps and AI tools
- Identify sensitive data used in prompts or workflows
- Correlate data exposure with user activity and permissions
- Use solutions like Reco’s data exposure management to prioritize high-risk interactions











%201.svg)









.svg)