Malicious Extensions That Lock You Out While They Steal Your Session



In early 2026, security researchers uncovered a coordinated campaign targeting enterprise HR and ERP platforms. Five Chrome extensions, installed more than 2,300 times, masqueraded as productivity tools for Workday, NetSuite, and SuccessFactors.

Once installed, they exfiltrated session tokens, enabled direct account takeover, and prevented IT teams from accessing security controls to respond. In this blog post, we will examine what happened, why the attack worked, and how SaaS-native detection can catch session hijacking before attackers achieve their objectives.
The Attack - Credential Theft and Response Blocking
The extensions marketed themselves as enterprise productivity tools. DataByCloud 2, for example, promised "premium tools" for bulk account management through a polished dashboard. Tool Access 11 positioned itself as a security feature that "restricts access to special tools."
All five shared identical code structures and API patterns despite appearing under two different publishers. The Chrome Web Store listings looked legitimate, and nothing in the privacy policies hinted at what came next. Here's what they actually did:
1. Continuous cookie exfiltration
The extensions harvested session authentication cookies for Workday, NetSuite, and SuccessFactors, transmitting them to attacker-controlled endpoints every 60 seconds. Chrome alarm listeners and cookie-change monitors ensured tokens were continuously captured, even when users logged out and back in.
2. Admin page blocking
The extensions manipulated the DOM to block access to 56 administrative pages, including password resets, session revocation, 2FA device management, and security audit logs. When an admin tried to access these pages, the extensions detected the page title via XPath, wiped the content, and redirected to a malformed URL.
3. Session hijacking
The most advanced extension, Software Access, received stolen cookies from the C2 server and injected them into the attacker's browser using chrome.cookies.set(). This enabled direct account takeover without passwords or MFA, turning stolen tokens into active sessions.
Why It Worked - The Browser Is Your SaaS Perimeter
The attack succeeded because browser extensions operate with broad permissions and minimal oversight. These five extensions requested access to cookies, scripting, storage, and declarativeNetRequest across Workday, NetSuite, and SuccessFactors. The permissions looked routine. Users approved them without a second thought.
Once an extension has those permissions, it bypasses every other control. SSO becomes irrelevant when the attacker already has the session cookie. MFA is completed before the token is stolen. Network monitoring sees normal HTTPS traffic to a cloud API. There's nothing anomalous at the network layer.
This is the blind spot. The browser has become the de facto perimeter for SaaS security, but most organizations still treat it as an afterthought. Traditional architectures assume the network is the boundary. SSO and MFA protect the front door, firewalls and endpoint agents handle the rest. That model breaks down when employees access dozens of SaaS applications daily through browsers that run untrusted code.
SaaS sprawl makes the problem exponentially worse. The average enterprise runs hundreds of cloud applications, each representing another target, another set of session tokens, another integration point where trust is implicitly granted and rarely verified. One compromised browser can expose every SaaS application it touches.
How Reco Detects and Responds to Session Hijacking
The extensions blocked obvious response paths. Admins trying to revoke sessions or change passwords found those pages broken or redirected. The tactic was designed to buy time and extract maximum value.
This is where perimeter-based thinking fails. When attacks originate from within the browser, use legitimate session tokens, and actively interfere with response mechanisms, detection must operate at the SaaS layer itself.
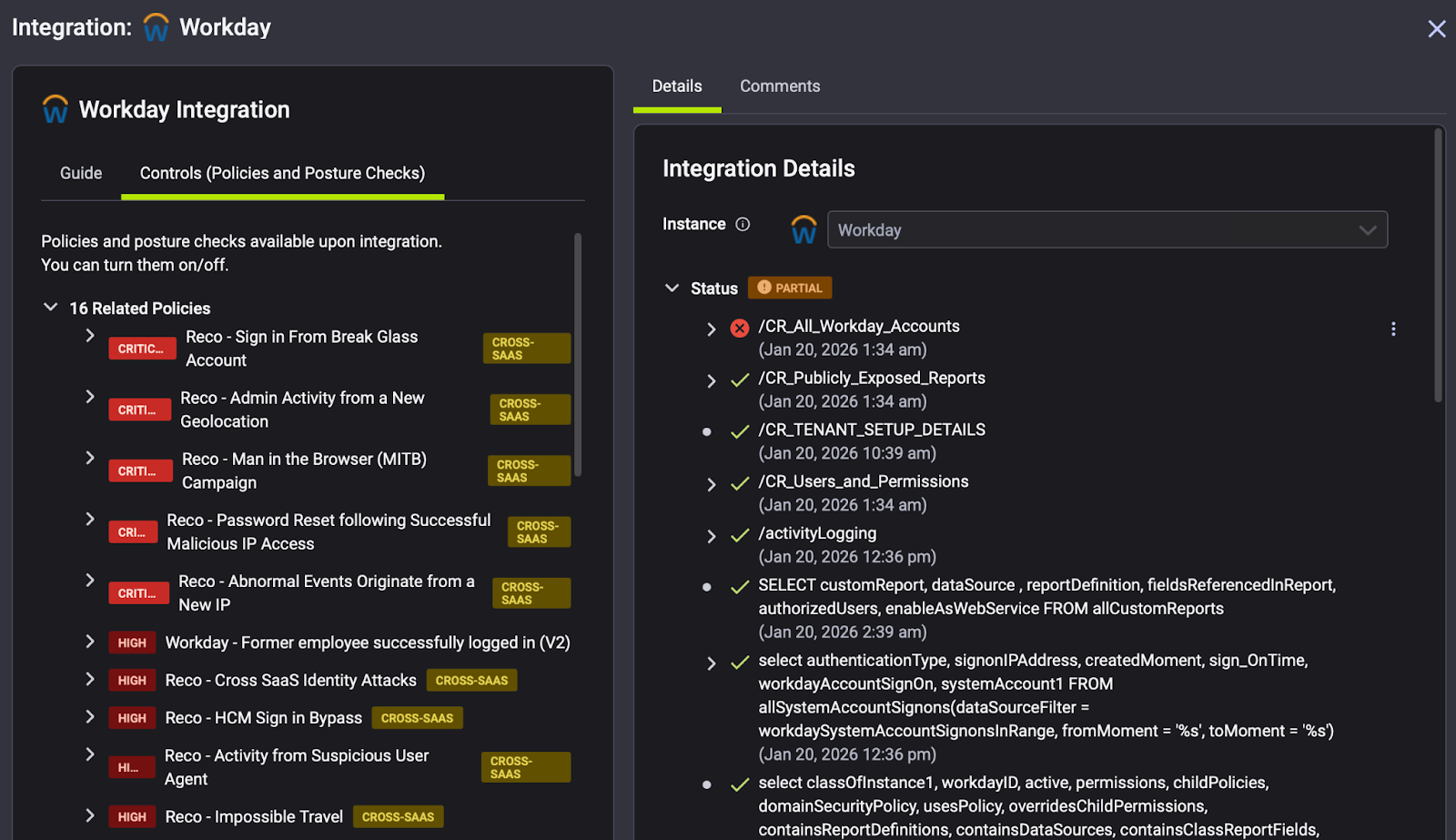
Reco's Dynamic SaaS Security platform is built for exactly this scenario: detecting identity compromise and enabling response even when traditional admin interfaces are unavailable.
1. Knowledge Graph Visibility
Reco's Knowledge Graph maps every identity, application, OAuth token, and data flow across your SaaS estate. Human identities, machine identities, SaaS-to-SaaS connections are all unified in a single view.
When a browser extension compromises a Workday session, the Knowledge Graph immediately reveals the blast radius: which other applications that identity can reach, what data they can access, and which integrations share those credentials.
This attack targeted users with access to Workday, NetSuite, and SuccessFactors simultaneously. The Knowledge Graph surfaces that concentration of privilege, flagging accounts with broad cross-platform access as high-value targets requiring additional monitoring.

2. Identity Threat Detection and Response
Reco's ITDR capabilities always monitor user behavior across SaaS applications to detect anomalies indicating compromise. The extensions harvested tokens every 60 seconds using Chrome alarm listeners and cookie-change monitors, then replayed those tokens from attacker infrastructure.
Reco catches this pattern through behavioral analytics and AI-powered correlation:
1. Impossible travel detection when a session appears from a new geography
2. Device anomalies when authentication originates from unrecognized infrastructure
3. Unusual access patterns when bulk data exports occur outside normal hours
Rather than generating isolated alerts, Reco correlates signals across applications to build complete threat narratives. Hundreds of pre-built detection rules cover account compromise, privilege escalation, and data exfiltration attempts out of the box.
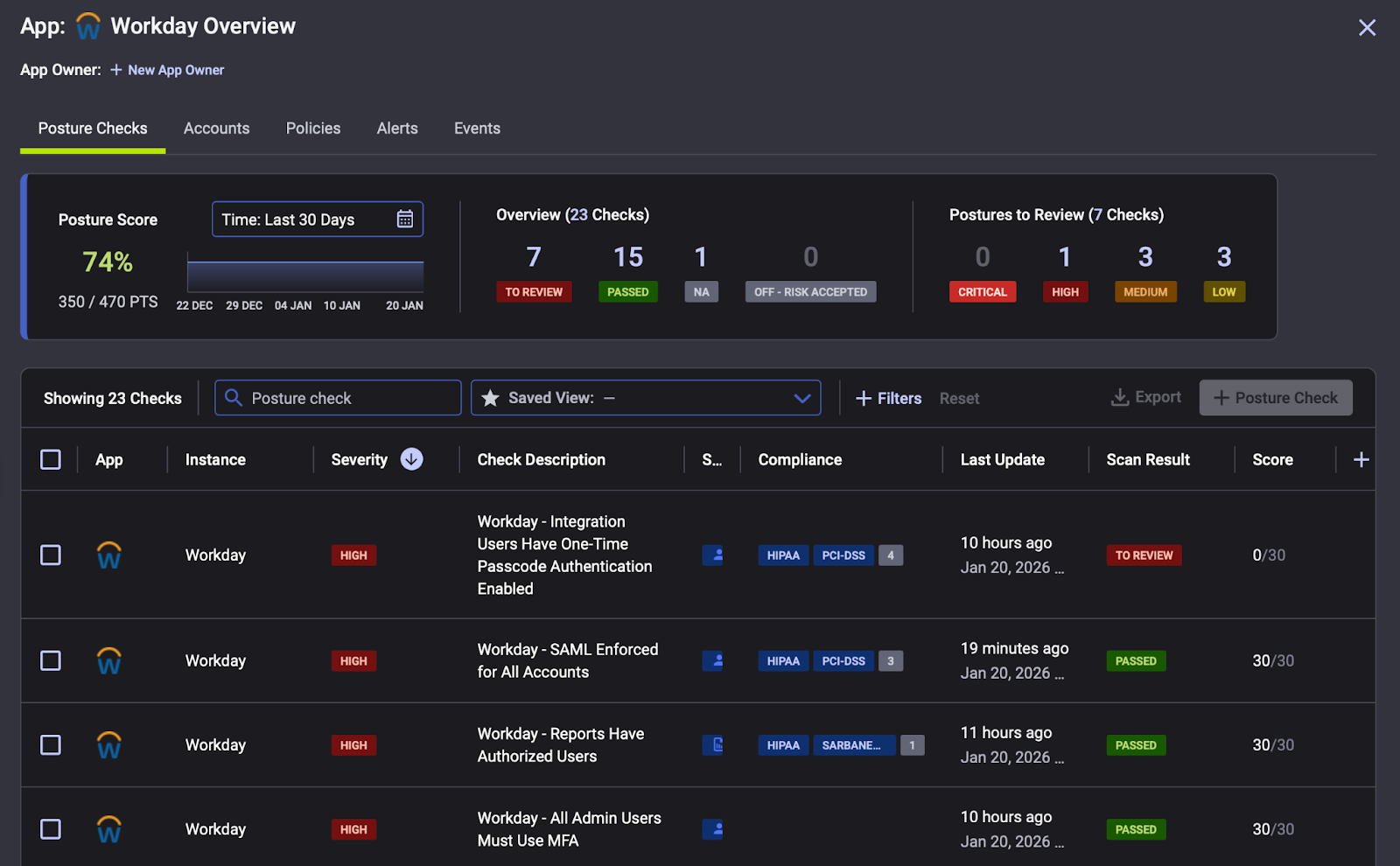
3. Automated Response via API Integration
The attackers blocked session management pages in Workday. But Reco doesn't depend on those interfaces.
SaaS platforms still record activity in their audit logs, and Reco connects directly to those platforms through secure API integrations. When ITDR detects a compromised session, automated workflows can revoke tokens, force MFA re-authentication, or disable accounts, all without touching the browser.
Reco integrates with 220+ SaaS applications, plus existing SIEM and SOAR platforms. Alerts route with full context. Response executes at machine speed, bypassing whatever controls the attacker has manipulated.
What This Means for Your SaaS Security Strategy
These five extensions represent a playbook we will see repeated: browser-based attacks on enterprise platforms with built-in anti-forensics to delay incident response. The extensions even included a hardcoded list of 23 Chrome extensions that they detected and reported to operators, identifying environments where their activity might be discovered.
Defense must match the sophistication of the attack. Reco provides the knowledge and visibility to understand the blast radius, the ITDR capabilities to catch impossible travel and anomalous behavior in real time, and the API integrations to revoke compromised sessions without relying on blocked admin interfaces.
Browser compromise does not have to mean SaaS compromise. Request a demo to see how Reco protects against session hijacking and SaaS identity threats.

Dr. Tal Shapira
ABOUT THE AUTHOR
Tal is the Cofounder & CTO of Reco. Tal has a Ph.D. from the school of Electrical Engineering at Tel Aviv University, where his research focused on deep learning, computer networks, and cybersecurity. Tal is a graduate of the Talpiot Excellence Program, and a former head of a cybersecurity R&D group within the Israeli Prime Minister's Office. In addition to serving as the CTO, Tal is a member of the AI Controls Security Working Group with the Cloud Security Alliance.
.png)
Tal is the Cofounder & CTO of Reco. Tal has a Ph.D. from the school of Electrical Engineering at Tel Aviv University, where his research focused on deep learning, computer networks, and cybersecurity. Tal is a graduate of the Talpiot Excellence Program, and a former head of a cybersecurity R&D group within the Israeli Prime Minister's Office. In addition to serving as the CTO, Tal is a member of the AI Controls Security Working Group with the Cloud Security Alliance.



%201.svg)











%201.svg)









.svg)