Introducing Full AI Agent Visibility for SaaS
.png)


Over the past twelve months, we have watched AI agents go from an emerging concept to a daily operational reality inside enterprise SaaS environments.
Organizations that were cautiously experimenting with ChatGPT plugins a year ago now have Salesforce Agentforce automating pipeline actions, Cursor generating production code through Model Context Protocol (MCP) connections, and custom n8n workflows triggering across dozens of integrated applications.
The speed of adoption has been remarkable, but the security visibility around it has not kept pace. Today we are launching Reco's AI agent security capability, giving security teams complete visibility and control over every AI agent operating across their SaaS ecosystem.
The AI Agent Blind Spot
Most security teams have spent years building visibility into their SaaS application stack. They know which apps are connected, who has access, and what permissions exist. That model worked when the entities interacting with your environment were humans and a manageable number of OAuth integrations. AI agents break that model completely.
Unlike a traditional SaaS plugin that sits in a defined scope with static permissions, an AI agent can act autonomously. It can read and write data across multiple systems, execute actions based on its own reasoning, and chain together capabilities in ways that were never explicitly authorized. A single Salesforce Agentforce agent might have access to CRM data, email, calendar, and Slack, and it will use all of those connections in service of whatever task it has been assigned.
The blast radius when something goes wrong extends to every system that agent touches.
Our data shows that the average SaaS application now has at least 10 AI agents associated with it. While most organizations track their connected applications in the hundreds, they have thousands of connected AI agents. The majority of these agents were connected by employees without security team involvement, making AI agents the center of how work gets done now, not a fringe concern at the edges of the enterprise.
Discovering Every AI Agent in Your Environment
Reco's AI agent security starts with discovery: the platform automatically inventories every AI agent operating across your connected SaaS applications, from well-known tools like ChatGPT, Claude, and Copilot to the embedded agents within platforms like Salesforce, ServiceNow, and HubSpot. For each agent, Reco maps which SaaS applications it connects to, what permissions it holds, who authorized it, and what data it can access.
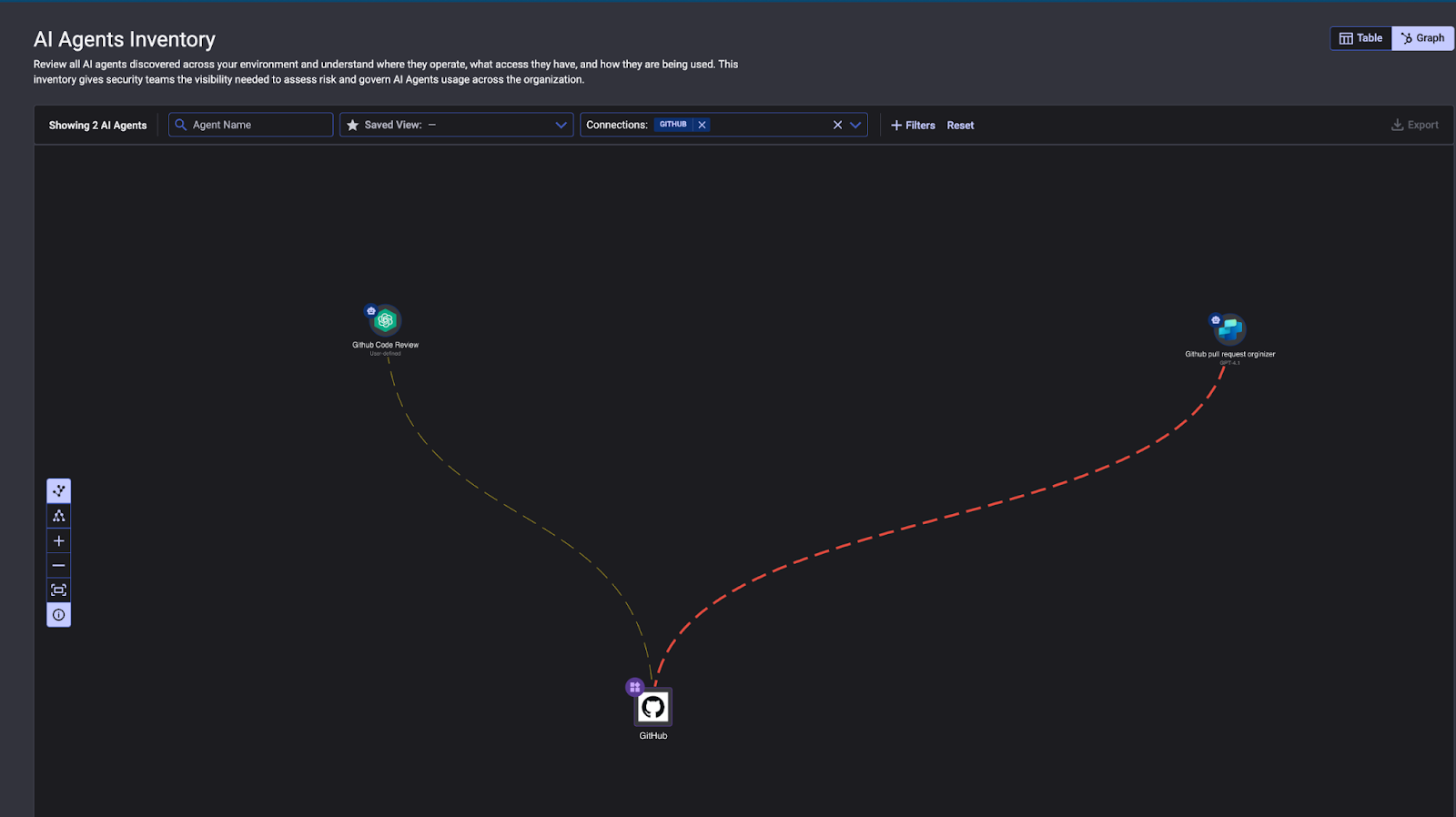
The AI agents inventory provides a graph-based view of every AI agent Reco discovers associated with a connected SaaS application. Here, two AI agents, a GitHub Code Review agent and a GitHub Pull Request Organizer, are mapped alongside their connections to GitHub. Security teams can filter by connection type, application, or risk level to focus on the agents that matter most.
Mapping Toxic Combinations
But discovery alone is not enough: AI agents create relationships between systems, and those relationships can produce permission breakdowns that no single application owner would authorize. We call these toxic combinations, and they are a direct consequence of how AI agents operate across SaaS boundaries.
Reco's Knowledge Graph maps these relationships in real time. It traces how AI agents, users, applications, and permissions connect to one another, surfacing patterns that would be invisible in a per-application security model.
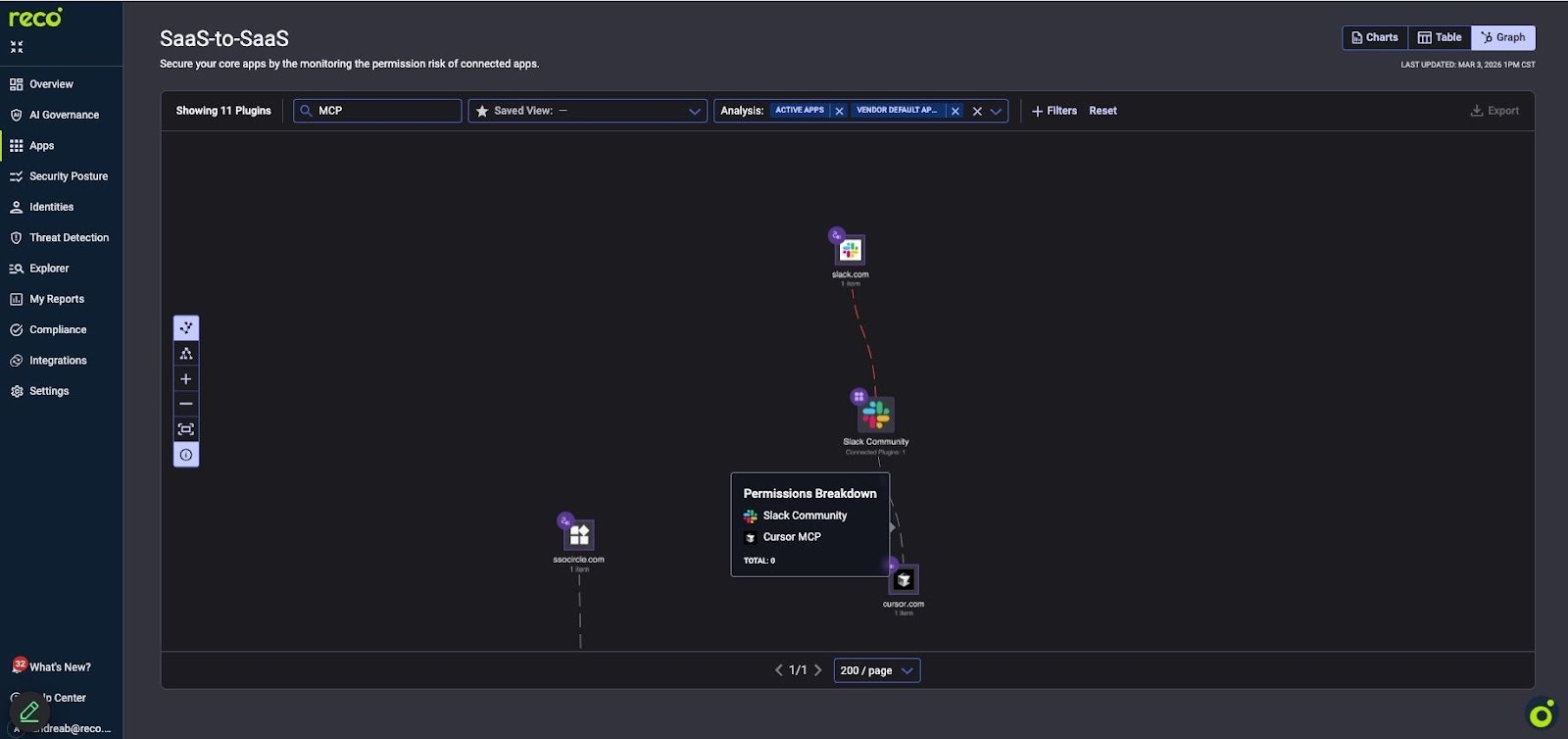
In this example above, Reco surfaced a toxic combination. An MCP server created a connection between Slack and Cursor, producing a permissions breakdown where two applications share a trust relationship that neither was designed to support. This is the type of connection that appears across enterprise environments as AI agents bridge systems together through MCP, OAuth grants, and API integrations.
The same pattern applies at scale. An AI agent connected to Google Drive and Salesforce creates a data path between document storage and CRM records. An automation tool linked to Slack and a code repository exposes internal communications to a development pipeline. Each connection is individually rational, but the aggregate effect is a web of trust relationships that no security policy explicitly defined and no traditional tool can map.
This is the supply chain risk that MCP introduces. The protocol was designed to let AI agents connect to external tools and data sources, and it does that efficiently. The problem is that every MCP connection creates a new trust boundary between systems, and those boundaries are largely invisible to traditional security tools. Reco makes them visible, showing exactly which systems are connected, what data flows between them, and where permission breakdowns exist.
Keeping Pace with AI Agent Sprawl
Those trust boundaries multiply every time an employee connects a new agent, and that is happening daily. New AI agents appear across SaaS environments constantly, employees connect them to corporate systems without filing a ticket, and the permission structures they create compound over time. Any security solution that requires manual onboarding or per-agent configuration will always be behind this adoption curve.
Reco's approach is built around the SaaS App Factory™, which integrates new applications in three to five days and maps them into the platform immediately. As new AI tools, agents, or MCP connections appear across your environment, they are discovered, classified, and assessed automatically.
This is the same unified platform that organizations already use to manage their SaaS security posture, detect identity threats, and enforce AI governance policies. AI agent security extends naturally from the visibility that Reco's dynamic SaaS security platform has provided from the beginning: complete, real-time awareness of every identity, application, and connection in your SaaS ecosystem.
What This Means for Security Teams
Until now, most organizations had no way to monitor AI agents across their SaaS environment. Endpoint security detects processes running but cannot interpret agent behavior, network tools observe API calls but cannot distinguish legitimate automation from compromise, and identity systems see OAuth grants but don't flag AI agent connections as unusual.
Shadow AI discovery data continues to show that 91% of AI tools operate without IT approval, and AI agents are the fastest-growing category within that figure. Reco's AI agent security changes that.
The platform surfaces your entire AI agent footprint in minutes, maps every permission and data access path, and gives security teams the controls to determine which agents should be sanctioned, restricted, or blocked entirely. All from the same platform they already use to secure the rest of their SaaS stack.
We built Reco to close the SaaS security gap. AI agents are the newest and fastest-growing dimension of that gap, and today's launch ensures our customers have the visibility to stay ahead of it.
Book a demo to find out what AI agents are already operating in your environment.
.png)
Andrea Bailiff-Gush
ABOUT THE AUTHOR
Andrea is the Head of Marketing of Reco, responsible for driving demand and growth in SaaS security. Andrea is a cyber security veteran, having supported various security companies across various growth milestones, from Seed round to acquisition. She is passionate about growing businesses and teams to drive profitable outcomes and better well being for CISOs and security practitioners.
.png)
Andrea is the Head of Marketing of Reco, responsible for driving demand and growth in SaaS security. Andrea is a cyber security veteran, having supported various security companies across various growth milestones, from Seed round to acquisition. She is passionate about growing businesses and teams to drive profitable outcomes and better well being for CISOs and security practitioners.



%201.svg)











%201.svg)









.svg)