


Shadow AI now adds approximately $670,000 to the cost of a breach when it is present, and it appears in roughly one in five incidents. That number comes from IBM’s 2025 Cost of a Data Breach Report, published last July across 600 organizations in 17 industries. It is not a projection. It reflects what organizations have already paid in higher breach costs associated with unmanaged AI usage.
Despite that, most CISOs still present shadow AI risk to finance teams in tool counts, threat severity levels, and policy coverage percentages. None of those metrics connect to a line on the balance sheet. A CFO cannot approve a budget against a threat level.
The conversation fails before it starts because security teams and finance teams speak different languages. IBM reports that 63% of organizations do not have formal AI governance policies, which means most companies are operating within the average $4.4M breach cost range while carrying additional exposure tied to uncontrolled AI-driven data access, without a financial model for what that means or what it costs to reduce.
The fix is not better slides. It is a different calculation.
This article provides a calculation framework, validated cost benchmarks, and a translation model to convert shadow AI findings into a financial narrative that supports budget decisions.
Walk into a CFO meeting with “71% of employees use unauthorized AI tools,” and you will get acknowledgment, not action. It describes behavior, not financial exposure.
Walk in with “current shadow AI exposure maps to a $4.63M expected breach cost, with a modeled reduction to $3.96M for a defined investment,” and the discussion shifts immediately. You are no longer describing risk. You are quantifying it.
The difference is not persuasion; it is alignment with how financial decisions are made. CFOs operate on expected value. They assess probability-weighted loss against the cost of reducing that loss. Security teams rarely frame risk this way. They present inventories, control coverage, and severity ratings that do not translate into financial impact or capital allocation.
IBM’s 2025 Cost of a Data Breach report provides the missing linkage. It quantifies cost differentials based on shadow AI exposure and the maturity of AI security controls. That allows security leaders to move from describing tool usage to modeling how uncontrolled access pathways increase breach cost, and how targeted investment reduces that exposure.
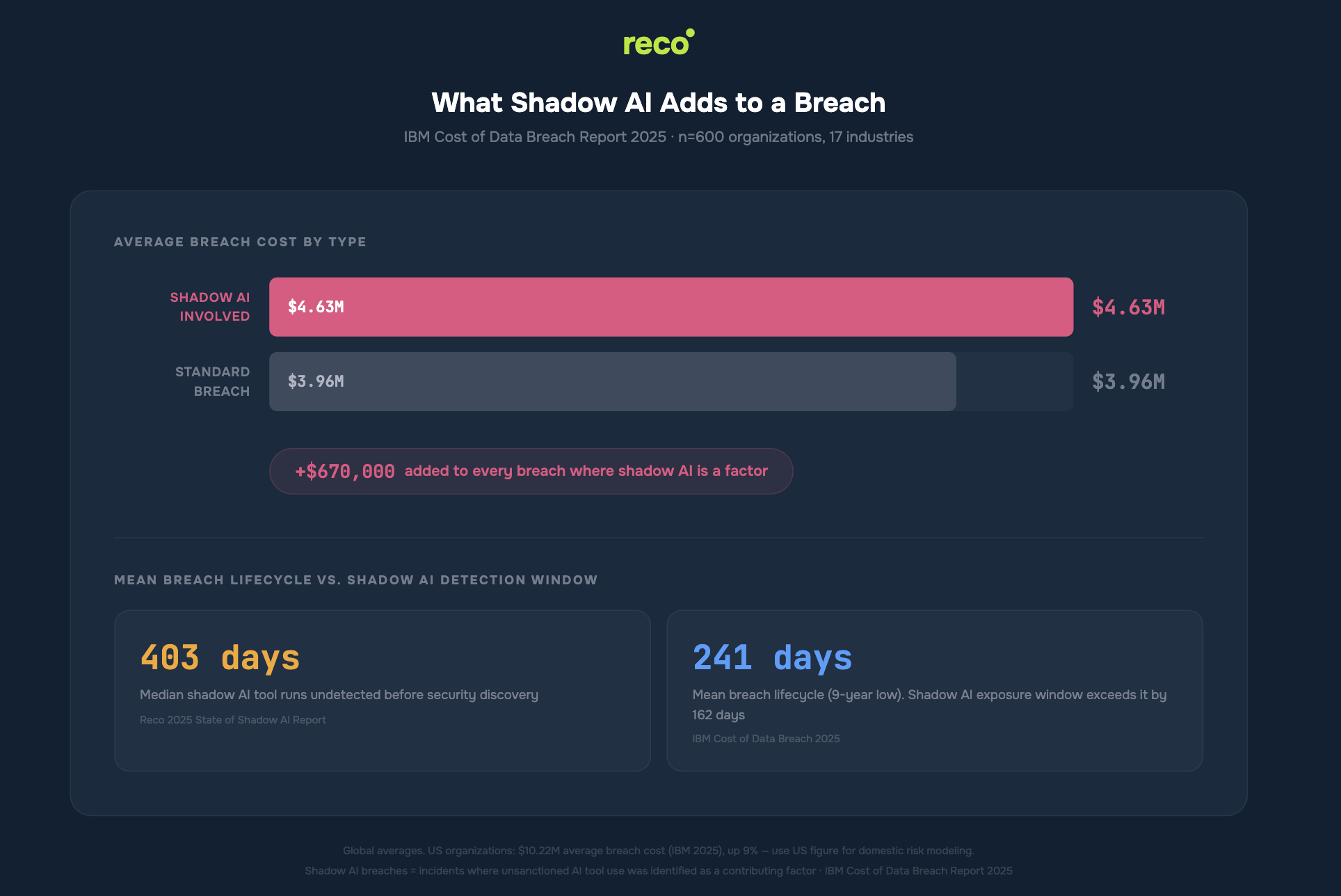
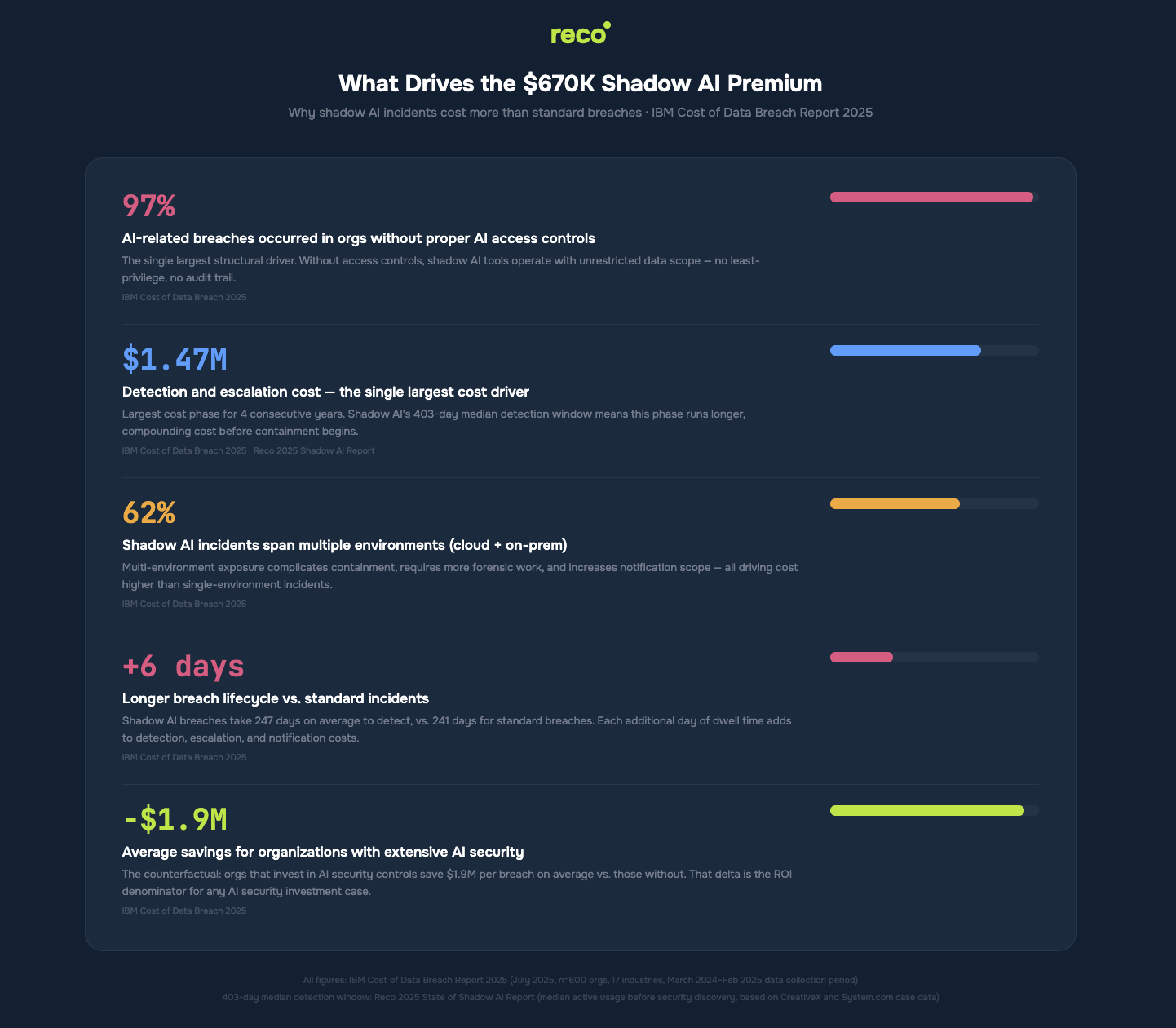
The $670K is not an abstraction. It reflects measurable cost drivers that map directly to gaps in access control, visibility, and containment, each of which can be addressed through targeted investment.
Lack of access control. IBM 2025 reports that 97% of AI-related breaches occurred in organizations without proper AI access controls. This is the structural failure point. Without enforced controls, shadow AI tools operate with broad and unmanaged data access, bypassing least-privilege principles, auditability, and containment boundaries.
Extended detection and escalation costs. IBM identifies detection and escalation as the most expensive phase of a breach, averaging $1.47M for the fourth consecutive year. Reco’s 2025 data shows that unauthorized AI tools remain active for a median of 403 days before detection, extending the exposure window and increasing the cost accumulation before containment begins.
Security maturity differential. The inverse is equally clear. IBM 2025 shows that organizations with extensive AI security and automation capabilities reduced breach costs by an average of $1.76M per incident compared to those without. This is not modeled savings. It is the observed cost difference between environments with mature controls and those operating without them.
You need four inputs and the IBM baseline:
IBM Cost of Data Breach Report 2025 · Reco 2025 State of Shadow AI Report
With those inputs, the conversation becomes: “Our current exposure is modeled at approximately $[IBM baseline plus the $670K shadow AI cost differential], weighted by breach probability based on our current detection window. Reducing that window from 403 days to near real-time detection decreases the exposure duration and shifts expected loss toward the $3.96M baseline. At [solution cost], the expected annual risk reduction is [cost differential multiplied by probability], representing a [ROI multiple] return on investment.”
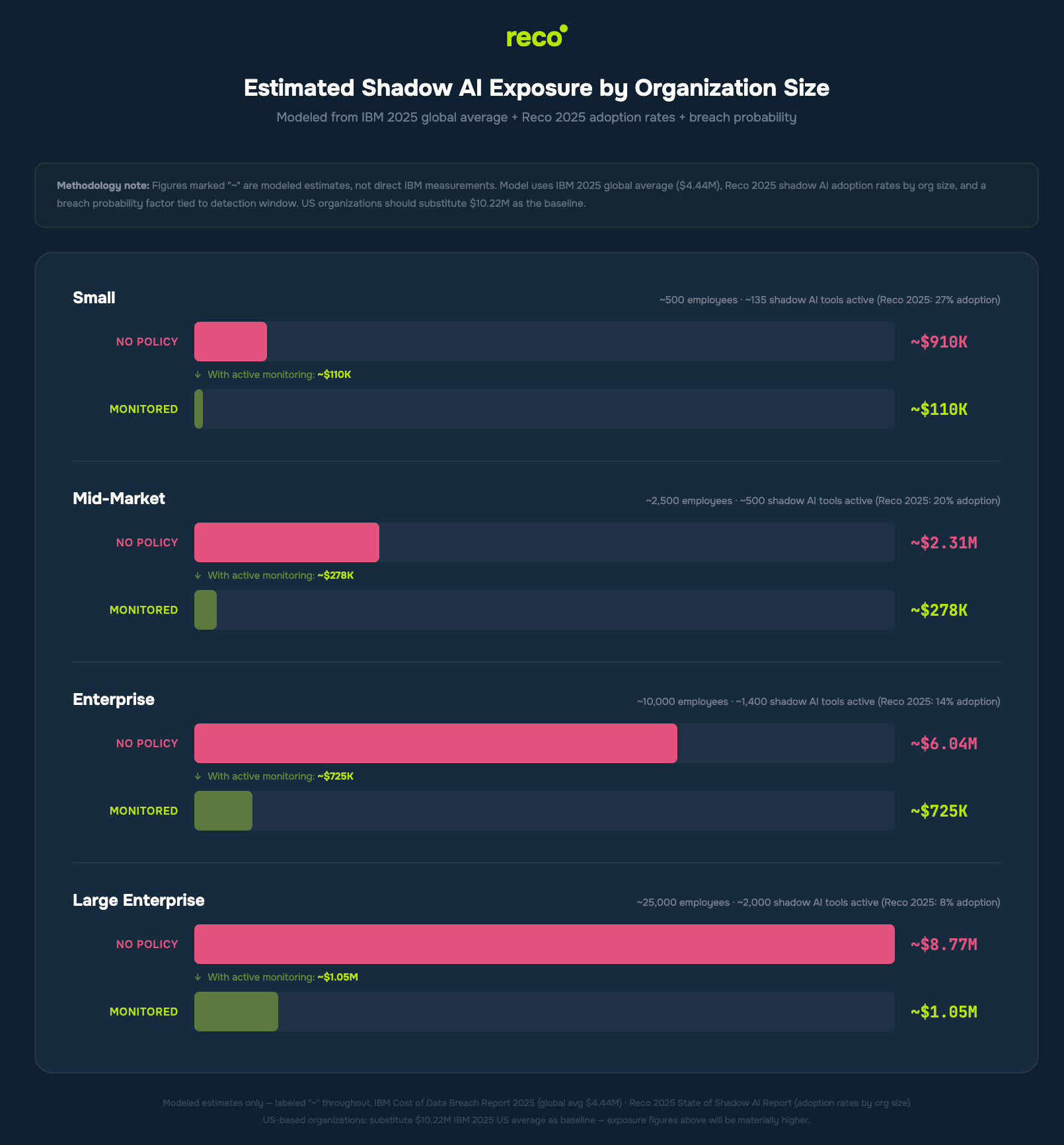
Most CISOs frame governance coverage as a compliance metric. That framing does not hold in a CFO conversation. The correct frame is financial: every AI tool operating outside governance introduces unpriced exposure on the balance sheet. Governance coverage is the variable that influences where your organization falls relative to IBM’s $670K cost differential associated with shadow AI.
IBM 2025 outlines measurable cost differences across AI security and governance maturity levels. The gap between limited or no governance and environments with continuous discovery and control is not a maturity score. It is an observed cost differential of approximately $1.76M per breach event, which should be treated as a direct input into the investment case.

Once you have the numbers, the delivery is four sentences:
“Shadow AI is present in approximately 20% of data breaches and is associated with an additional $670K in breach costs, according to IBM’s 2025 research. Our current environment includes [X] tools operating without governance, with a detection window of approximately [Y] days, placing us within the higher-cost exposure profile observed by IBM at $4.63M. Reducing that window through continuous monitoring decreases exposure duration and shifts expected loss toward the $3.96M baseline. At [solution cost], the expected annual risk reduction is [cost differential multiplied by probability], representing a [ROI multiple] return on investment.”
Four sentences. Verified numbers. A clear ask.
The most difficult input in this model is the tool count. Without continuous discovery, that number remains an estimate. Reco’s Knowledge Graph provides visibility into active AI tools across the environment, including shadow AI accessed through OAuth integrations and browser extensions, and maps each to its associated data access scope. This shifts the output from a list of applications to a view of which tools can access customer PII, source code, or financial records, and the level of exposure associated with that access.
This distinction matters in a CFO conversation because it replaces estimated exposure with measurable exposure. “We estimate approximately 500 shadow AI tools” does not carry the same weight as “We have 487 active shadow AI tools, of which 34 have write access to production data, representing $X in modeled exposure.”
The difference between approval and deferral is the precision of the underlying numbers.
The gap between security insight and budget approval is not awareness. It is quantification. Shadow AI expands data access beyond governed boundaries, increasing exposure in ways traditional metrics do not capture. When that exposure is expressed in expected financial terms, the conversation shifts from risk discussion to investment decision. CFOs do not fund tool adoption. They fund measurable risk reduction.
The organizations that succeed will be those that can translate uncontrolled access into modeled loss and reduction into clear financial return. In an environment where shadow AI continues to grow, precision in measurement is what determines which risks are addressed and which are deferred.

Gal is the Cofounder & CPO of Reco. Gal is a former Lieutenant Colonel in the Israeli Prime Minister's Office. He is a tech enthusiast, with a background of Security Researcher and Hacker. Gal has led teams in multiple cybersecurity areas with an expertise in the human element.
