


Most CISOs are asking the wrong question. They focus on how many unauthorized AI tools are running in their environment. That number is real, it is often large, and it matters. But it is not the number that drives budget approval or changes behavior at the board level.
The better question is financial: what does your current shadow AI exposure represent in annual expected breach impact? That is a number that can be modeled, presented, and acted on. According to IBM’s 2025 Cost of a Data Breach Report, it is a number most security teams are not quantifying in financial terms.
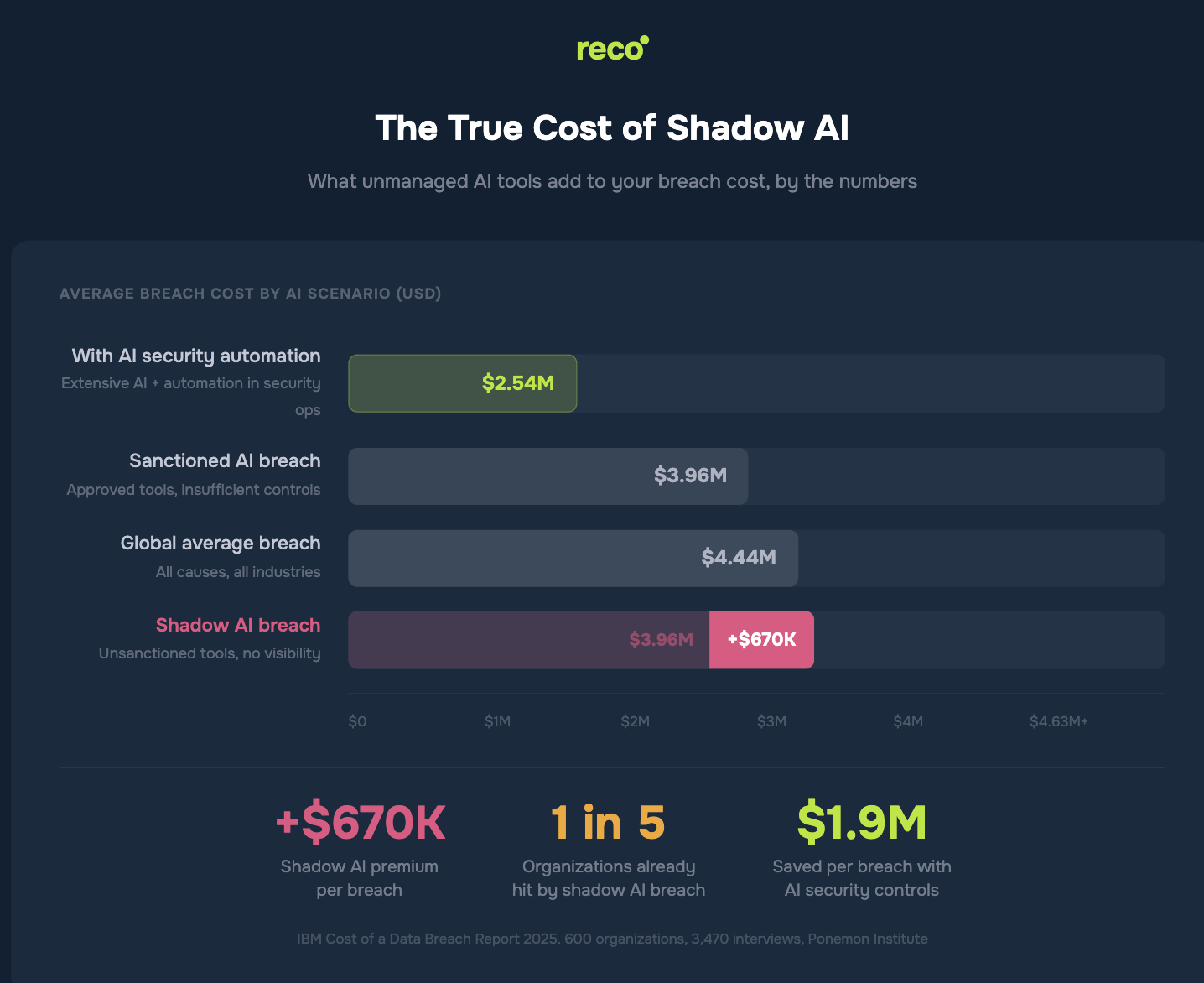
Breaches involving shadow AI are associated with approximately $670,000 in additional costs and appear in roughly 20% of incidents. IBM also reports that 97% of organizations experiencing AI-related breaches lacked the access controls required to manage that risk. These figures point to a consistent pattern: unmanaged access drives higher financial impact.
Here is what your annual shadow AI exposure looks like when translated into measurable financial terms.
This article translates IBM’s 2025 breach data into a cost framework CISOs can use in budget conversations, and explains the drivers behind the $670K cost differential.
Security teams often present shadow AI risk as a compliance or policy issue. It appears in reports as a count of unauthorized tools. The board interprets it as an IT hygiene problem, something to address in a future cycle.
IBM’s 2025 data reframes the issue. Shadow AI is associated with materially higher breach costs, with an average increase of approximately $670K when present. This is not a compliance signal. It is a measurable financial exposure tied to unmanaged data access.
The expected value calculation follows directly from this. When unmanaged AI-driven access is present, the associated cost differential can be modeled against the likelihood of exposure within the environment. For example, applying a 20% risk weighting to the $670K cost differential produces an estimated $134K in annualized exposure. For US organizations, where the average breach cost reaches $10.22M, the same modeling approach results in significantly higher potential impact.
The premium is not driven by more sophisticated attacks. It is driven by delayed detection. Shadow AI breaches take seven days longer to identify and contain than the global average. That additional week is where costs begin to compound.
Longer containment means more data is accessed, more systems are affected, and more extensive forensics are required. The data involved is also more sensitive: 65% of shadow AI breaches compromise PII, compared to 53% for standard incidents. Intellectual property is exposed in 40% of cases, versus 33% globally.
This is not incidental. Employees using unauthorized AI tools are typically processing real operational data, including documents, customer information, and internal analysis. These tools require data to function, which creates direct data flows into external systems. In this context, usefulness and exposure are effectively the same action.
IBM found that 97% of organizations that experienced an AI-related breach lacked proper access controls at the time. In most cases, the impact is not driven by the incident alone, but by a governance gap that allows exposure to persist and expand.
Approximately 63% of breached organizations have no AI governance policy in place. Among those that do, only 34% actively audit for unsanctioned AI. This implies that only a small portion of organizations are systematically identifying shadow AI, while the majority discover it reactively through breaches, audit findings, or regulatory inquiries.
Most coverage of this data focuses on the risk side. The more useful read is the upside: IBM reports that organizations with extensive use of AI and automation in security operations see average breach costs of approximately $3.62M, a reduction of roughly $1.9M compared to organizations not using these technologies.
The gap between visibility and no visibility is measurable. IBM quantified it across hundreds of organizations. Investments in AI-driven detection and continuous monitoring do not eliminate breaches, but they reduce time to identification and containment, lowering the total cost per incident.
That reframes the budget conversation entirely. Not “we need to find shadow AI,” but “improving visibility and control can reduce breach cost by nearly $2M per incident, and our current exposure reflects the absence of that visibility.”
The structural problem with shadow AI is not malicious intent. It is speed. An employee can connect an unauthorized AI tool to a business application in minutes, while security teams operating on periodic review cycles may not detect it for months.
Continuous discovery compresses the detection window from months to hours. This reduces exposure duration and limits the likelihood that unauthorized access leads to a full breach scenario, shifting expected loss away from the $4.63M cost profile associated with unmanaged environments.
The $670K cost differential is closely tied to delayed detection and extended exposure. Reco’s Discovery Engine continuously monitors OAuth authorizations, API connections, and SaaS logs, surfacing unauthorized AI tools within minutes of first use. When an employee connects a new AI tool to a business application, security teams gain immediate visibility into the user, the application, the data access scope, and the duration of activity.
This level of visibility is not achievable through periodic audits. It aligns with the type of continuous monitoring and control maturity associated with lower breach costs in IBM’s 2025 data, where organizations with advanced AI security and automation capabilities report significantly reduced financial impact per incident.
Shadow AI is no longer a visibility issue, but a measurable financial exposure that most organizations have yet to quantify. IBM’s data makes the cost of that exposure explicit, from the $670K differential to the multi-million dollar impact of unmanaged access. The difference between organizations that absorb that cost and those that reduce it is not awareness. It is the ability to model expected loss and act on it with precision.
Platforms like Reco enable that shift by turning shadow AI activity into measurable exposure, giving security teams the data required to align with financial decision-making. In an environment where AI-driven access continues to expand, the teams that quantify exposure will control both the narrative and the budget.

Gal is the Cofounder & CPO of Reco. Gal is a former Lieutenant Colonel in the Israeli Prime Minister's Office. He is a tech enthusiast, with a background of Security Researcher and Hacker. Gal has led teams in multiple cybersecurity areas with an expertise in the human element.
