A Hacker’s Guide to a SaaS Application Breach



In cybersecurity, the most successful practitioners are the ones who understand that to have even a chance at success, you have to think like the threat actors do. And while Sun Tzu certainly never could have imagined what any piece of even the phrase “SaaS Security” could possibly mean, his ancient advice to “know the enemy” is still salient.
Today, let’s get to know our enemy. We are going to walk through the phases of an attack through the eyes of a hacker trying to compromise a SaaS environment, step by step. We’ll also go through how, at each step, Reco’s SaaS security can foil “us,” aka, the threat actor trying to steal data through the complicated web of SSO and non-SSO SaaS applications.
So put on your best disguises and get ready to start thinking like the bad guys.
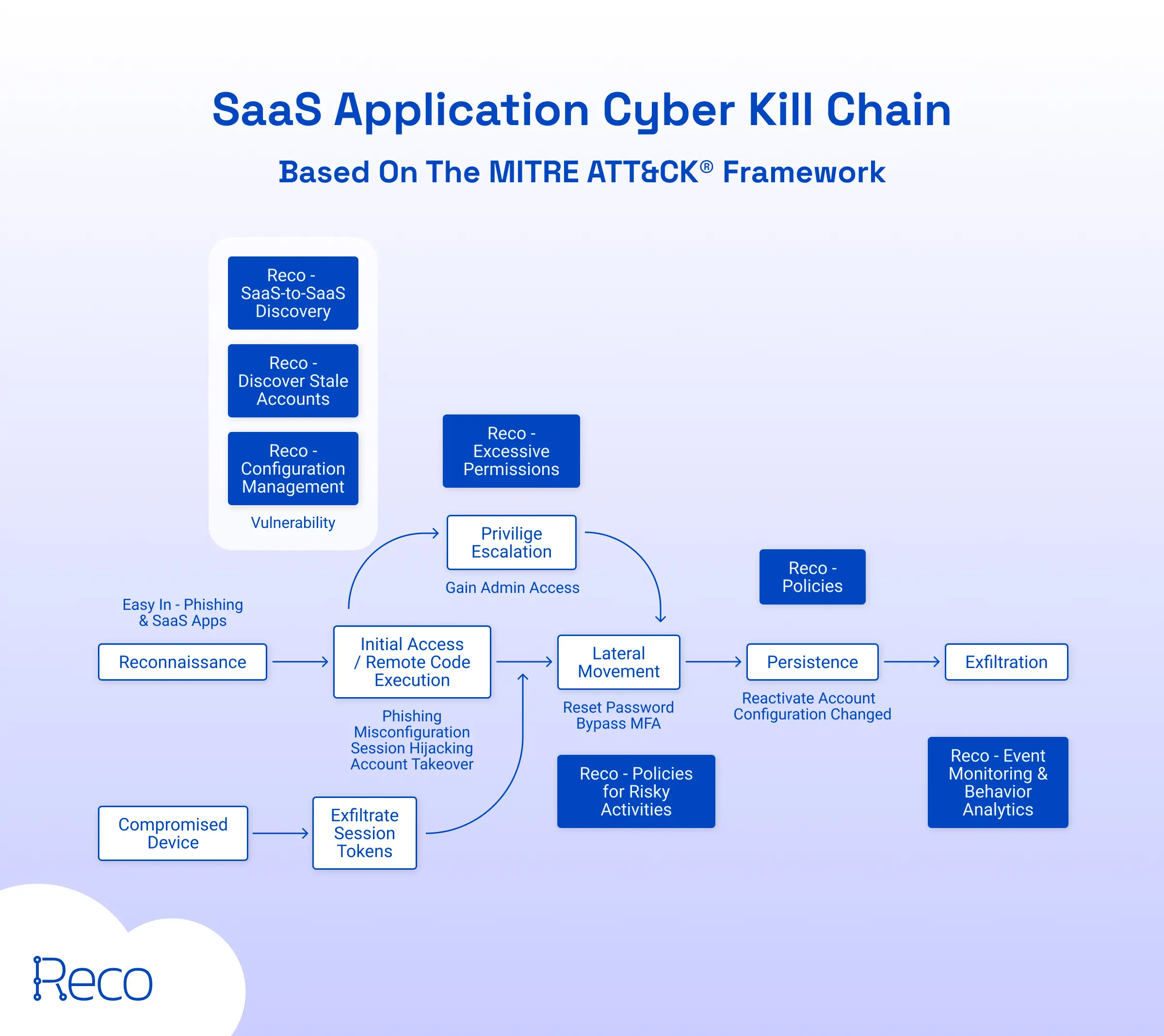
Phase 1: Reconnaissance
Your first step on your SaaS hacking journey is how most crimes start: reconnaissance. You need to identify your target(s), and make a plan of how you’re going to infiltrate .
During this phase, you’re going to try to gain as much information as possible, such as IP addresses, domains, emails, what systems they use, known vulnerabilities of those systems to use later on, or any other information you can use to gain a foothold into your target’s digital assets. It turns out that hackers also take the advice to “know the enemy.”
Luckily, this is often made almost easy for you, since almost every company and every person’s information is somewhere on the internet. A quick search for employees on LinkedIn can give you scores of useful information that you can then leverage in a few ways. The most recent hack of the MGM Resorts is one of the most high profile examples of how threat actors used LinkedIn to scope out the names and information of high access users they could then later use to their advantage by calling into the support line and getting a reset on all MFA credentials of privileged users.
Phase 2: Initial Access/Remote Code Execution
Now it’s time for your reconnaissance efforts to pay off and you’re ready to start your digital misdeeds. Because organizations now use a wide variety of SaaS applications, this initial access can happen multiple ways. A few examples you might consider exploring on your hacker journey are:
- Phishing/social engineering to gain access
- Stolen credentials reused from another attack (available on the dark web)
- Misconfigurations in SaaS applications
- Session hijacking
- Account takeover
- Zero-day exploits
- One-day exploits (or unpatched vulnerabilities)
Foiled by Reco:
Drats! Your target has Reco and has been alerted to your suspicious activity. Some of the ways Reco might stop you at Phase 1 are:
- Configuration Management: Continuous monitoring for security configuration drifts that might have changed over time but left holes threat actors can exploit.
- Stale Account Management: Reco’s app governance tools monitor for stale or inactive accounts that could be left accidentally open for threat actors to exploit as an access point.
- App-to-App Discovery: SaaS applications often talk to other SaaS applications in the background, allowing threat actors to slide in unnoticed, but Reco’s monitoring makes sure those unusual activities are discovered immediately.
Loophole: Phase 2 Workaround
Sure, you might go through the traditional steps to gain access and a foothold, but you might also be tempted to skip those steps. This requires you to compromise a device and then exfiltrate session tokens. Nobody said hacking would be easy: even ten years ago a large breach would only require one zero-day attack, and now you’ll need an average of five.
Phase 3: Privilege Escalation
You’ve made it in. Unfortunately, your way in might not have full admin access to all the most valuable files, so now you will need to find a way to elevate your privileges. For example, you might gain entry to an employee’s laptop, but you’ll need access all the way to the servers to access the most valuable information.
Foiled by Reco:
If the attacked organization has Reco, they’ll be automatically alerted to unusual access activities such as users suddenly receiving excessive permissions. These types of events and chains of events also trigger alerts in the SaaS security monitoring.
Phase 4: Lateral Movement
Now that you’ve gained admin (or even root!) access to the systems, you need to find the digital crown jewels. This requires traversing the environment, moving through and trying to find where valuable data is stored, while also resetting passwords and bypassing MFA policies.
Foiled by Reco:
Organizations with Reco can implement policies for risky activities (or use Reco’s preset policies) that alert for activities such as password resets on admin accounts.
Phase 5: Persistence
This is where the rubber really meets the road in your hacking journey: persistence. It’s one thing to find ways in and exist in memory, it’s another entirely to deploy code that can outlast a reboot. During this phase, you might want to reactivate old/dormant accounts (perhaps of former employees) to blend in with normal activities that might not draw the alerts of other monitoring systems, or change configurations so they don’t throw alerts as you continue your attacks.
Foiled by Reco:
You’ve done well on your first try as a threat actor, but Reco is still one step ahead. Reco’s monitoring and policy alerts would let the organization you have in your sights know about account reactivations and configuration changes that disable alerts. By the time you’ve reached this stage, other monitoring and alerting tools struggle to find this type of advanced, persistent attack. Reco’s AI-informed alerting won’t miss it.
Phase 6: Exfiltration
This part of your hacking journey is what you’ve been working for this whole time: the precious data you can exfiltrate and either sell or hold for ransom payments. Often you can leverage SaaS apps and vulnerabilities to get massive amounts of data out quickly, as we saw in the MOVEit attacks in 2023.
Foiled by Reco:
Unfortunately for your hacking journey, your hard work still isn’t enough. Reco’s event monitoring and behavior analysis alerts organizations when it finds unusual activity from both users and applications, such as large file downloads or exfiltrations. This last line of defense can be the difference between a cybersecurity scare and cybersecurity disaster, since the files threat actors are looking for won’t be removed from their intended locations.
Summary
You did your best at being bad, and fortunately for the rest of us, your best wasn’t good enough. No matter where you were in the SaaS attack kill chain, Reco was a step ahead.
As threat actors advance their attacks on increasingly complex systems, hiding themselves with more complex methods, Reco can find them and alert organizations of all sizes of suspicious activities. Organizations rely on SaaS applications to do business in the modern world, and threat actors are ready to take advantage of these complex webs of dependencies. Don’t let them.
To find out more about how Reco SaaS security prevents threat actors at all stages in the SaaS attack chain, request a demo to learn more.

Gal Nakash
ABOUT THE AUTHOR
Gal is the Cofounder & CPO of Reco. Gal is a former Lieutenant Colonel in the Israeli Prime Minister's Office. He is a tech enthusiast, with a background of Security Researcher and Hacker. Gal has led teams in multiple cybersecurity areas with an expertise in the human element.

Gal is the Cofounder & CPO of Reco. Gal is a former Lieutenant Colonel in the Israeli Prime Minister's Office. He is a tech enthusiast, with a background of Security Researcher and Hacker. Gal has led teams in multiple cybersecurity areas with an expertise in the human element.



%201.svg)











%201.svg)









.svg)